inner workings of the hacking group by providing a rare insight
into the “behind-the-scenes look into their methods.”
IBM’s X-Force Incident Response Intelligence Services (IRIS) got
hold of nearly five hours worth of video recordings of the
state-sponsored group it calls ITG18 (also called
Charming Kitten, Phosphorous, or APT35[1]) that it uses to train
its operators.
Some of the victims in the videos included personal accounts of
U.S. and Greek Navy personnel, in addition to unsuccessful phishing
attempts directed against U.S. state department officials and an
unnamed Iranian-American philanthropist.
“Some of the videos showed the operator managing adversary-created
accounts while others showed the operator testing access and
exfiltrating data from previously compromised accounts,” the
researchers
said.
The IBM researchers said they found the videos on a virtual
private cloud server that was left exposed due to a
misconfiguration of security settings. The server, which was also
found to host several ITG18 domains earlier this year, held more
than 40 gigabytes of data.
targets’ email and social media credentials obtained via spear-phishing,
using the information to log in to the accounts, delete
notifications of suspicious logins so as not to alert the victims,
and exfiltrate contacts, photos, and documents from Google Drive.
“The operator was also able to sign into victims’ Google Takeout
(takeout.google.com), which allows a user to export content from
their Google Account, to include location history, information from
Chrome, and associated Android devices,” the researchers
noted.
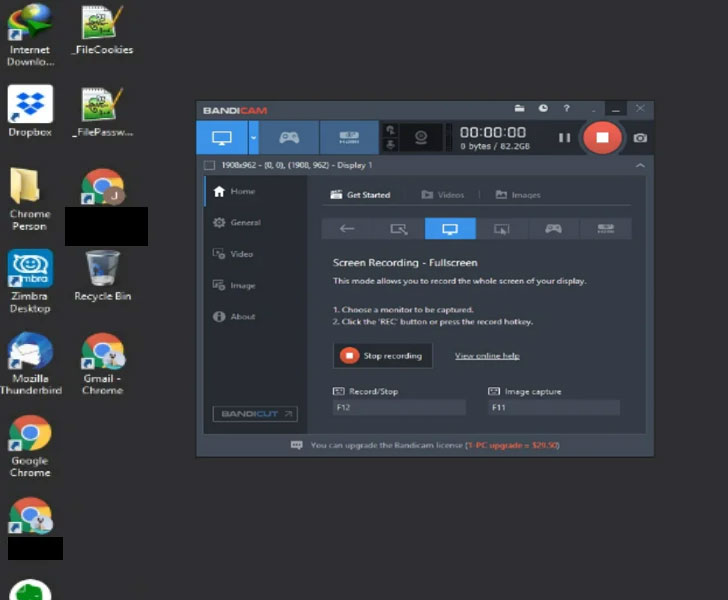
Besides this, the videos — captured using Bandicam’s
screen-recording tool — also show that the actors behind the
operation plugged the victims’ credentials to Zimbra’s email
collaboration software intending to monitor and manage the
compromised email accounts.
Outside of email accounts, the researchers said they found the
attackers employing a long list of compromised usernames and
passwords against at least 75 different websites ranging from banks
to video and music streaming to something as trivial as pizza
delivery and baby products.
accounts, which include a phone number with Iran’s country code
(+98), using them to send the phishing emails, some of which
bounced back, suggesting the emails did not reach the victim’s
inbox.
“During the videos where the operator was validating victim
credentials, if the operator successfully authenticated against a
site that was set up with multi-factor authentication (MFA) they
paused and moved on to another set of credentials without gaining
access,” the researchers said.
ITG18 has a long history of targeting the U.S. and the Middle
Eastern military, diplomatic, and government personnel for
intelligence gathering and espionage to serve Iran’s geopolitical
interests.
If anything, the discovery emphasizes the need to secure your
accounts by using stronger passwords, turning on two-factor
authentication, and reviewing and limiting access to third-party
apps.
“The compromise of personal files of members of the Greek and
U.S. Navy could be in support of espionage operations related to
numerous proceedings occurring in the Gulf of Oman and Arabian
Gulf,” IBM X-Force researchers concluded. “The group has shown
persistence in its operations and consistent creation of new
infrastructure despite multiple public disclosures and broad
reporting on its activity.”
References
- ^
APT35
(malpedia.caad.fkie.fraunhofer.de) - ^
researchers
(securityintelligence.com) - ^
spear-phishing
(www.clearskysec.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/AGojF6xrBSA/iranian-hacking-training-videos.html