As businesses move to a remote workforce, hackers have increased
their activity to capitalize on new security holes. Cybercriminals
often use unsophisticated methods that continue to be extremely
successful.
These include phishing emails to harvest credentials and gain
easy access to business-critical environments.
Hackers are also using ransomware to hold your data hostage,
demanding a ransom payment in exchange for a decryption key that
unlocks your stolen data.
When dealing with a cyberattack, there are practical steps you
want to follow.
What do these steps include?
- Quickly contain and isolate critical systems
- Report the hack to your customers and business
stakeholders - Engage the help of law enforcement
- Enact your disaster recovery and business continuity plans
- Analyze the attack, and remediate
Quickly contain and isolate critical systems
This first step is necessary: quickly contain and isolate
critical systems. There is a chance that if you discover ransomware
or other evidence of the hack on your network, it may not have made
it to all business-critical data and systems.
Isolate known infected clients from the network as soon as
possible. This action prevents any change the infection or
malicious code will spread from the isolated clients.
Using a systematic approach of isolation, and containment, while
cleaning up the infection, is one of the best ways to regain
control of the network and eliminate lingering malicious code.
Report the hack to your customers and business
stakeholders
Time and again, organizations are judged based on how they
handle situations where a system hack or data breach has occurred.
Reporting security incidents is always the best approach.
Organizations suffer negative consequences for any type of coverups
or delays in disclosing information.
While not pleasant to do so, disclosing security incidents as
quickly as possible creates an atmosphere of transparency that
generally reflects well on the organization in the long run.
Organizations may be liable under compliance regulations to report
any breach of security as well.
Engage the help of law enforcement
If your business is a victim of a cyberattack, engaging with law
enforcement is an important step. Law enforcement agencies such as
the Federal Bureau of Investigation (FBI) in the United States can
open the door to various resources to help with the aftermath of
the attack.
The FBI and other organizations can help investigate
cyberattacks and intrusions. They work to collect and share
intelligence[1] for the greater good,
unmasking individuals and groups responsible for malicious cyber
activities.
Alerting these agencies of a cyberattack can promote the greater
good of bringing cybercriminals to justice.
Enact your disaster recovery and business continuity plans
It is essential to develop an effective disaster recovery plan
as part of your overall business continuity plan. The disaster
recovery plan outlines the steps needed to operate the business
with degraded systems or missing business-critical data.
After discovering a hack of your business, the disaster recovery
plan should be enacted. These plans reestablish business continuity
as soon as possible. They also get everyone on the same page for
streamlining business processes, even in a degraded state.
Analyze the attack, and remediate
After system integrity has returned to normal and the imminent
security threat has been removed, businesses will want to analyze
the attack and remediate any vulnerabilities.
This root/cause analysis will help to determine any weaknesses
in the cybersecurity posture.
Organizations need to assess weaknesses in security
continuously. No matter how large or small, any type of breach or
successful attack should be used to understand where the security
posture can be improved.
Improving password security – a necessary step
Compromised credentials are a significant root cause of modern
data breaches. IBMs Cost of a Data
Breach Report 2020[2]
noted:
“One in five companies (19%) that suffered a malicious data
breach was infiltrated due to stolen or compromised credentials,
increasing the average total cost of a breach for these companies
by nearly $1 million to $4.77 million. Overall, malicious attacks
registered as the most frequent root cause (52% of breaches in the
study), versus human error (23%) or system glitches (25%), at an
average total cost of $4.27 million.”
Organizations must bolster account security, including
preventing weak or breached passwords used in the environment. All
too often, end-users choose vulnerable passwords. Hackers often use
previously breached passwords that are readily available on the web
in password spraying attacks and other account-based attacks.
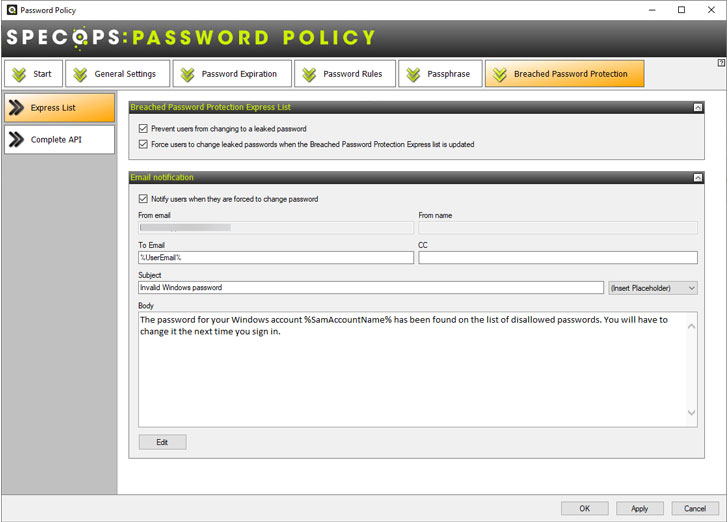 |
| Configuring breached password protection in Specops Password Policy |
There are very few Active Directory tools, and capabilities
found natively to implement the proper protections for businesses
to protect user accounts. Specops Password Policy secures Active
Directory credentials by blocking the use of leaked passwords in the
environment.[3]
Wrapping Up
Data breaches, ransomware infections, and other types of hacks
are all too common for businesses today. These ultimately lead to
credential leaks.
Organizations must implement effective cybersecurity
protections, including protecting against weak passwords in the
environment. Specops Password Policy is a solution that helps
organizations to get a handle on password security in Active
Directory.
Learn more about Specops Password Policy, and download a free
trial version here[4].
References
- ^
collect
and share intelligence (www.fbi.gov) - ^
Cost of
a Data Breach Report 2020 (www.ibm.com) - ^
blocking
the use of leaked passwords in the environment.
(specopssoft.com) - ^
here
(specopssoft.com)