Cybersecurity researchers have disclosed a new class of
vulnerabilities impacting major DNS-as-a-Service (DNSaaS) providers
that could allow attackers to exfiltrate sensitive information from
corporate networks.
“We found a simple loophole that allowed us to intercept a
portion of worldwide dynamic DNS traffic going through managed DNS
providers like Amazon and Google,” researchers Shir Tamari and Ami
Luttwak from infrastructure security firm Wiz said[1].
Calling it a “bottomless well of valuable intel,” the treasure
trove of information contains internal and external IP addresses,
computer names, employee names and locations, and details about
organizations’ web domains. The findings were presented[2]
at the Black Hat USA 2021 security conference last week.
“The traffic that leaked to us from internal network traffic
provides malicious actors all the intel they would ever need to
launch a successful attack,” the researchers added. “More than
that, it gives anyone a bird’s eye view on what’s happening inside
companies and governments. We liken this to having nation-state
level spying capability – and getting it was as easy as registering
a domain.”
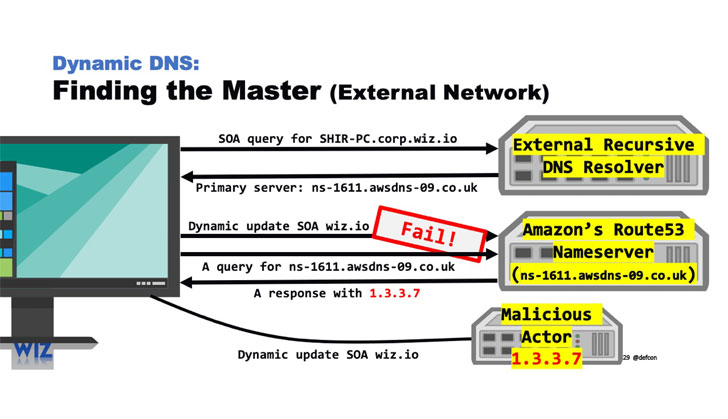
The exploitation process hinges on registering a domain on
Amazon’s Route53 DNS service (or Google Cloud DNS) with the same
name as the DNS name server — which provides the translation (aka
resolution) of domain names and hostnames into their corresponding
Internet Protocol (IP) addresses — resulting in a scenario that
effectively breaks the isolation between tenants, thus allowing
valuable information to be accessed.
In other words, by creating a new domain on the Route53 platform
inside AWS name server with the same moniker and pointing the
hosted zone to their internal network, it causes the Dynamic DNS
traffic from Route53 customers’ endpoints to be hijacked and sent
directly to the rogue and same-named server, thus creating an easy
pathway into mapping corporate networks.
“The dynamic DNS traffic we wiretapped came from over 15,000
organizations, including Fortune 500 companies, 45 U.S. government
agencies, and 85 international government agencies,” the
researchers said. “The data included a wealth of valuable intel
like internal and external IP addresses, computer names, employee
names, and office locations.”
While Amazon and Google have since patched the issues, the Wiz
research team has also released a
tool[3] to let companies test if
their internal DDNS updates are being leaked to DNS providers or
malicious actors.