Cybersecurity teams from Microsoft on Saturday disclosed they
identified evidence of a new destructive malware operation
targeting government, non-profit, and information technology
entities in Ukraine amid brewing geopolitical tensions between the
country and Russia.
“The malware is disguised as ransomware but, if activated by the
attacker, would render the infected computer system inoperable,”
Tom Burt, corporate vice president of customer security and trust
at Microsoft, said[1], adding the intrusions
were aimed at government agencies that provide critical executive
branch or emergency response functions.
Also targeted is an IT firm that “manages websites for public
and private sector clients, including government agencies whose
websites
were recently defaced[2],” Burt noted.
The computing giant, which first detected the malware on January
13, attributed the attacks to an emerging threat cluster codenamed
“DEV-0586,” with no observed overlaps in tactics
and procedures to other previously documented groups. It further
said the malware was found on dozens of impacted systems, a number
it expects to increase as the investigation continues.
According to Microsoft Threat Intelligence Center (MSTIC) and
Microsoft Digital Security Unit (DSU), the attack
chain[3] is a two-stage process
that entails —
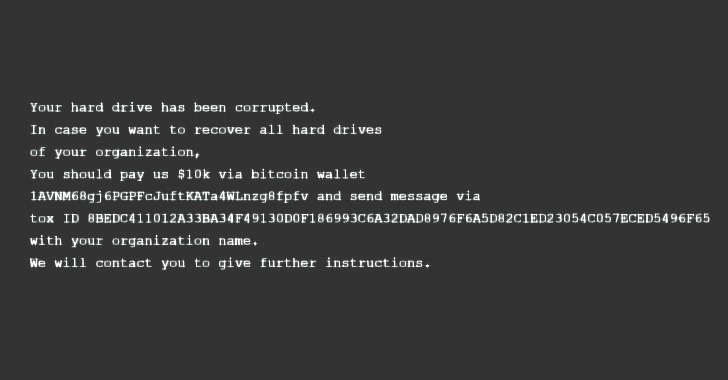
- Overwriting the Master Boot Record (MBR[4]), the first sector of
any hard disk that identifies where the operating system is located
in the disk so that it can be loaded into a computer’s RAM, on a
victim’s system to display a fake ransom note urging the target to
pay an amount of $10,000 to a bitcoin wallet - A second-stage executable that retrieves a file corrupter
malware hosted on a Discord channel that’s designed to search for
files with 189 different extensions, then irrevocably overwrite
their contents with a fixed number of 0xCC bytes and rename each
file with a seemingly random four-byte extension.
The malicious activity is “inconsistent” with cybercriminal
ransomware activity for reasons that “explicit payment amounts and
cryptocurrency wallet addresses are rarely specified in modern
criminal ransom notes” and “the ransom note in this case does not
include a custom ID,” Microsoft said.
The development comes as numerous government websites in the
Eastern European country were defaced
on Friday[5] with a message warning
Ukrainians that their personal data was being uploaded to the
Internet. The Security Service of Ukraine (SSU) said it found
“signs” of involvement of hacking groups associated with the
Russian intelligence services.
“Given the scale of the observed intrusions, MSTIC is not able
to assess intent of the identified destructive actions but does
believe these actions represent an elevated risk to any government
agency, non-profit or enterprise located or with systems in
Ukraine,” the researchers cautioned.
However, Reuters earlier today raised
the possibility[6]
that the attacks may have been the work of an espionage group
linked to Belarusian intelligence that’s tracked as UNC1151 and
Ghostwriter. “Multiple significant intrusions into Ukrainian
government entities have been conducted by UNC1151,” cybersecurity
firm Mandiant disclosed[7]
in a report in November 2021, pointing out the group’s operations
as those aligned with Belarusian government interests.
References
- ^
said
(blogs.microsoft.com) - ^
websites were recently defaced
(thehackernews.com) - ^
attack chain
(www.microsoft.com) - ^
MBR
(en.wikipedia.org) - ^
defaced on Friday
(thehackernews.com) - ^
raised the possibility
(www.reuters.com) - ^
disclosed
(www.mandiant.com)
Read more https://thehackernews.com/2022/01/a-new-destructive-malware-targeting.html