Numerous Windows machines located in South Korea have been
targeted by a botnet tracked as PseudoManuscrypt since at
least May 2021 by employing the same delivery tactics of another
malware called CryptBot.
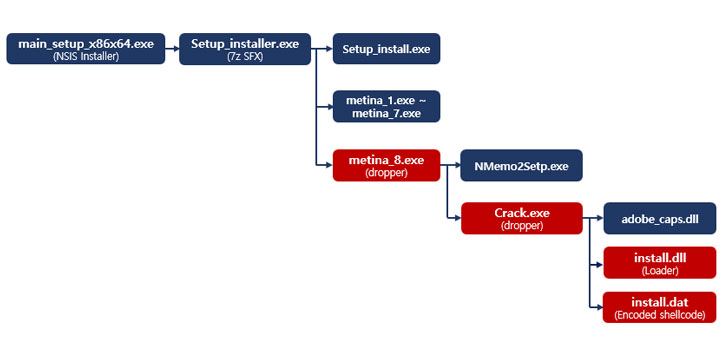
“PseudoManuscrypt is disguised as an installer that is similar
to a form of CryptBot[1], and is being
distributed,” South Korean cybersecurity company AhnLab Security
Emergency Response Center (ASEC) said[2] in a report published
today.
“Not only is its file form similar to CryptBot, but it is also
distributed via malicious sites exposed on the top search page when
users search commercial software-related illegal programs such as
Crack and Keygen,” it added.
According to ASEC, around 30 computers in the country are being
consistently infected on a daily basis on average.
PseudoManuscrypt was first documented by Russian cybersecurity
firm Kaspersky in December 2021, when it disclosed[3]
details of a “mass-scale spyware attack campaign” infecting more
than 35,000 computers in 195 countries globally.
Targets of PseudoManuscrypt attacks, which it originally
uncovered in June 2021, include a significant number of industrial
and government organizations, including enterprises in the
military-industrial complex and research laboratories, in Russia,
India, and Brazil, among others.
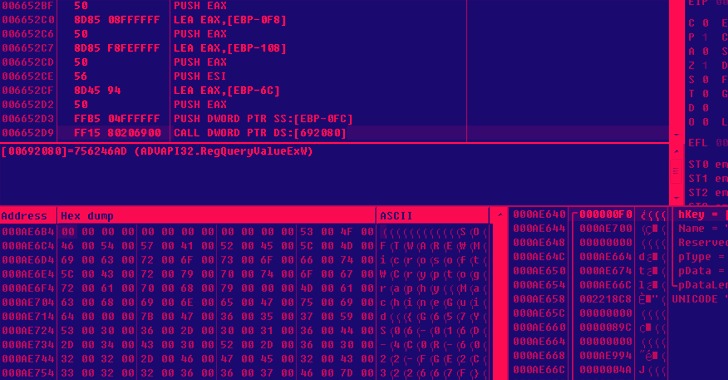
The main payload module is equipped with extensive and varied
spying functionality that provides the attackers with virtually
full control of the infected system. It includes stealing VPN
connection details, recording audio with the microphone, and
capturing clipboard contents and operating system event log
data.
Furthermore, PseudoManuscrypt can access a remote
command-and-control server under the attacker’s control to carry
out various nefarious activities such as file download, execute
arbitrary commands, log keypresses, and capture screenshots and
videos of the screen.
“As this malware is disguised as an illegal software installer
and is distributed to random individuals via malicious sites, users
must be careful not to download relevant programs,” the researchers
said. “As malicious files can also be registered to service and
perform continuous malicious behaviors without the user knowing,
periodic PC maintenance is necessary.”
References
Read more https://thehackernews.com/2022/02/pseudomanuscrypt-malware-spreading-same.html