The maintainers of the NGINX web server project have issued
mitigations to address security weaknesses in its Lightweight
Directory Access Protocol (LDAP[1]) Reference
Implementation.
“NGINX Open Source and NGINX Plus are not themselves affected,
and no corrective action is necessary if you do not use the
reference implementation,” Liam Crilly and Timo Stark of F5
Networks said[2]
in an advisory published Monday.
NGINX said that the reference implementation[3], which uses LDAP to authenticate users[4], is impacted only under
three conditions if the deployments involve –
- Command-line parameters to configure the Python-based reference
implementation daemon - Unused, optional configuration parameters, and
- Specific group membership to carry out LDAP authentication
Should any of the aforementioned conditions be met, an attacker
could potentially override the configuration parameters by sending
specially crafted HTTP request headers and even bypass group
membership requirements to force LDAP authentication to succeed
even when the falsely authenticated user does’t belong to the
group.
As countermeasures, the project maintainers have recommended
users to ensure that special characters are stripped from the
username field in the login form presented during authentication
and update appropriate configuration parameters with an empty value
(“”).
The maintainers also stressed that the LDAP reference
implementation mainly “describes the mechanics of how the
integration works and all of the components required to verify the
integration” and that “it is not a production‑grade LDAP
solution.”
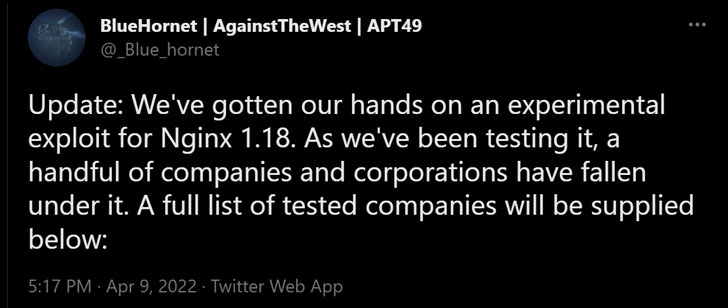
The disclosure comes after details[5]
of the issue emerged in the public domain over the weekend when a
hacktivist group called BlueHornet said[6]
it had “gotten our hands on an experimental exploit for NGINX
1.18.”
References
Read more https://thehackernews.com/2022/04/nginx-shares-mitigations-for-zero-day.html