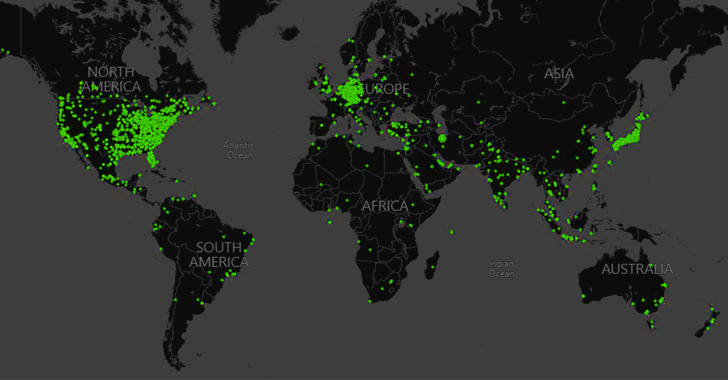
Microsoft and a consortium of cybersecurity companies took legal
and technical steps to disrupt the ZLoader botnet, seizing
control of 65 domains that were used to control and communicate
with the infected hosts.
“ZLoader is made up of computing devices in businesses,
hospitals, schools, and homes around the world and is run by a
global internet-based organized crime gang operating malware as a
service that is designed to steal and extort money,” Amy
Hogan-Burney, general manager of Microsoft’s Digital Crimes Unit
(DCU), said[1].
The operation, Microsoft said, was undertaken in collaboration
with ESET, Lumen’s Black Lotus Labs, Palo Alto Networks Unit 42,
Avast, Financial Services Information Sharing and Analysis Center
(FS-ISAC), and Health Information Sharing and Analysis Center
(H-ISAC).
As a result of the disruption, the domains are now redirected to
a sinkhole, effectively preventing the botnet’s criminal operators
from contacting the compromised devices. Another 319 backup domains
that were generated via an embedded domain generation algorithm
(DGA[2]) have also been
confiscated as part of the same operation.
ZLoader, like its notorious counterpart TrickBot[3], started off[4]
as a derivative of the Zeus banking trojan[5]
in November 2019 before undergoing active refinements and upgrades
that have enabled other threat actors to purchase the malware from
underground forums and repurpose it to suit their goals.
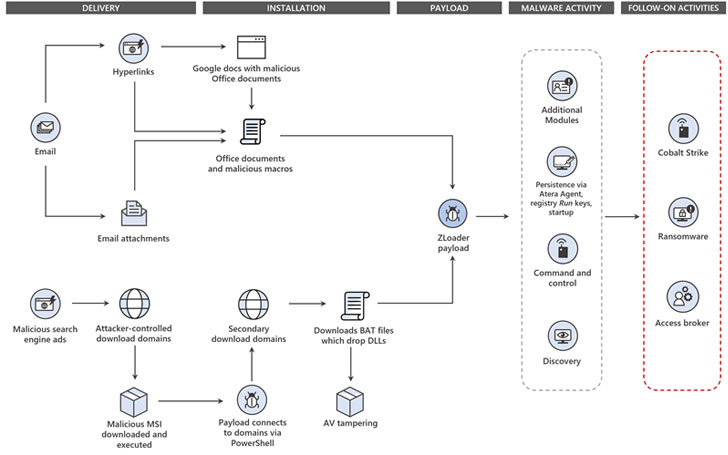
“ZLoader has remained relevant as attackers’ tool of choice by
including defense evasion capabilities, like disabling security and
antivirus tools, and selling access-as-a-service to other affiliate
groups, such as ransomware operators,” Microsoft said.
“Its capabilities include capturing screenshots, collecting
cookies, stealing credentials and banking data, performing
reconnaissance, launching persistence mechanisms, misusing
legitimate security tools, and providing remote access to
attackers.”
ZLoader’s transition from a basic financial trojan to a
sophisticated malware-as-a-service (MaaS) solution has also made it
possible for the operators to monetize the compromises by selling
the access to other affiliate actors, who then misuse it to deploy
additional payloads like Cobalt Strike and ransomware.
Campaigns involving ZLoader have abused[6]
phishing emails, remote management software, and rogue Google Ads
to gain initial access to the target machines, while simultaneously
using several complex tactics for defense evasion, including
injecting malicious code into legitimate processes.
Interestingly, an analysis of the malware’s malicious activities
since February 2020 has revealed that most of the operations
originated from just two affiliates since October 2020:
“dh8f3@3hdf#hsf23” and “03d5ae30a0bd934a23b6a7f0756aa504.”
While the former used “ZLoader’s ability to deploy arbitrary
payloads to distribute malicious payloads to its bots,” the other
affiliate, active to date, appears to have focussed on siphoning
credentials from banking, cryptocurrency platforms, and e-commerce
sites, Slovak cybersecurity firm ESET said[7].
To top it all, Microsoft also unmasked Denis Malikov, who lives
in the city of Simferopol on the Crimean Peninsula, as one of the
actors behind the development of a module used by the botnet to
distribute ransomware strains, stating that it chose to name the
perpetrator to “make clear that cybercriminals will not be allowed
to hide behind the anonymity of the internet to commit their
crimes.”
The takedown effort is reminiscent of a global operation to
disrupt the notorious TrickBot botnet[8] in October 2020.
Although the botnet managed to bounce back last year, it has since
been retired[9]
by the malware authors in favor of other stealthy variants such as
BazarBackdoor.
“Like many modern malware variants, getting ZLoader onto a
device is oftentimes just the first step in what ends up being a
larger attack,” Microsoft said. “The trojan further exemplifies the
trend of common malware increasingly harboring more dangerous
threats.”
References
- ^
said
(blogs.microsoft.com) - ^
DGA
(www.cybereason.com) - ^
TrickBot
(thehackernews.com) - ^
started
off (www.microsoft.com) - ^
Zeus
banking trojan (en.wikipedia.org) - ^
abused
(thehackernews.com) - ^
said
(www.welivesecurity.com) - ^
notorious TrickBot botnet
(thehackernews.com) - ^
retired
(thehackernews.com)
Read more https://thehackernews.com/2022/04/microsoft-disrupts-zloader-cybercrime.html