A threat group that pursues crypto mining and distributed
denial-of-service (DDoS) attacks has been linked to a new botnet
called Enemybot, which has been discovered enslaving routers and
Internet of Things (IoT) devices since last month.
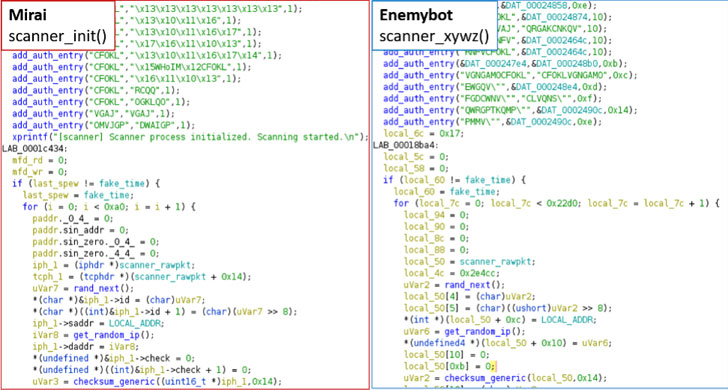
“This botnet is mainly derived from Gafgyt[1]‘s source code but has
been observed to borrow several modules from Mirai[2]‘s original source code,”
Fortinet FortiGuard Labs said[3]
in a report this week.
The botnet has been attributed to an actor named Keksec (aka
Kek Security[4], Necro, and FreakOut[5]), which has been linked
to multiple botnets such as Simps[6], Ryuk[7]
(not to be confused with the ransomware of the same name), and
Samael[8], and has a history of
targeting cloud infrastructure to carry out crypto mining and DDoS
operations.
Primarily targeting routers from Seowon Intech, D-Link, and iRZ
to propagate its infections and grow in volume, an analysis of the
malware
specimen[9] has highlighted
Enemybot’s obfuscation attempts to hinder analysis and connect to a
remote server that’s hosted in the Tor anonymity network to fetch
attack commands.
Enemybot, like the other botnet malware, is the result of
combining and modifying the source code of Mirai and Gafgyt, with
the latest version using the former’s scanner and bot killer
modules that are used to scan and terminate competitor processes
running on the same devices.
Some of the n-day vulnerabilities used by the botnet to infect
more devices are as follows –
- CVE-2020-17456[10] (CVSS score: 9.8) – A
remote code execution flaw in Seowon Intech SLC-130 And SLR-120S
devices. - CVE-2018-10823[11] (CVSS score: 8.8) – An
arbitrary code execution vulnerability in D-Link routers - CVE-2022-27226[12] (CVSS score: 8.8) – A
cross-site request forgery issue affecting iRZ Mobile Routers
leading to remote code execution
Fortinet also pointed out its overlaps with Gafgyt_tor[13], suggesting that
“Enemybot is likely an updated and ‘rebranded’ variant of
Gafgyt_tor.”
The disclosure comes as researchers from Qihoo 360’s Network
Security Research Lab (360 Netlab) detailed a rapidly spreading
DDoS botnet called Fodcha that has ensnared more than 10,000 daily
active bots, cumulatively infecting over 62,000 unique bots from
March 29 to April 10, 2022.
Fodcha has been observed spreading through known vulnerabilities
in Android, GitLab (CVE-2021-22205[14]), Realtek Jungle SDK
(CVE-2021-35394[15]), digital video
recorders from MVPower, LILIN, and routers from TOTOLINK and
ZHONE.
References
- ^
Gafgyt
(thehackernews.com) - ^
Mirai
(thehackernews.com) - ^
said
(www.fortinet.com) - ^
Kek
Security (nsfocusglobal.com) - ^
FreakOut
(thehackernews.com) - ^
Simps
(www.uptycs.com) - ^
Ryuk
(www.lacework.com) - ^
Samael
(www.lacework.com) - ^
malware specimen
(www.virustotal.com) - ^
CVE-2020-17456
(nvd.nist.gov) - ^
CVE-2018-10823
(nvd.nist.gov) - ^
CVE-2022-27226
(nvd.nist.gov) - ^
Gafgyt_tor
(blog.netlab.360.com) - ^
CVE-2021-22205
(thehackernews.com) - ^
CVE-2021-35394
(nvd.nist.gov)
Read more https://thehackernews.com/2022/04/new-enemybot-ddos-botnet-borrows.html