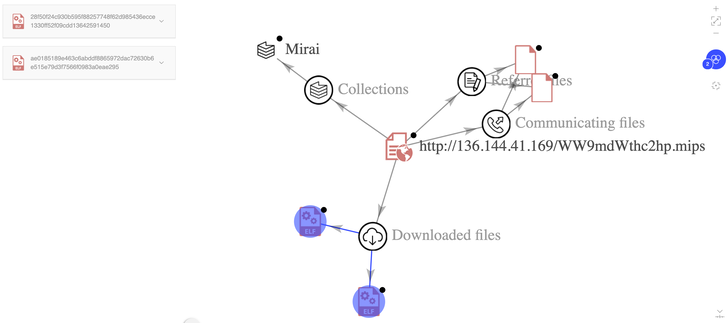
A new variant of an IoT botnet called BotenaGo has emerged in
the wild, specifically singling out Lilin security camera DVR
devices to infect them with Mirai malware.
Dubbed “Lilin Scanner[1]” by Nozomi Networks, the
latest version[2]
is designed to exploit a two-year-old critical command injection vulnerability[3] in the DVR firmware that
was patched by the Taiwanese company in February 2020.
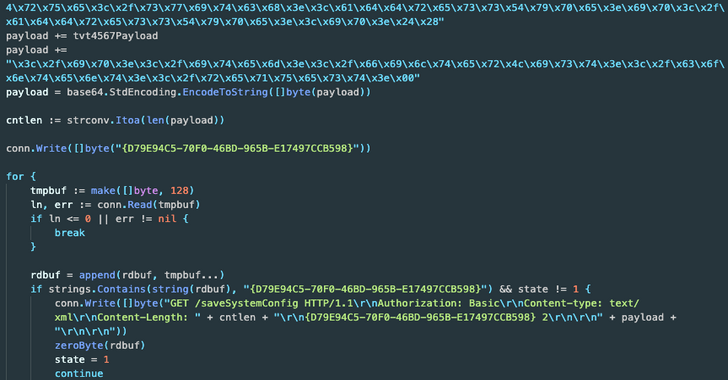
BotenaGo[4], first documented in
November 2021 by AT&T Alien Labs, is written in Golang and
features over 30 exploits for known vulnerabilities in web servers,
routers and other kinds of IoT devices.
The botnet’s source code has since been uploaded to GitHub,
making it ripe for abuse by other criminal actors. “With only 2,891
lines of code, BotenaGo has the potential to be the starting point
for many new variants and new malware families using its source
code,” the researchers said[5]
this year.
The new BotenaGo malware is the latest[6]
to exploit vulnerabilities in Lilin DVR devices after Chalubo,
Fbot, and Moobot. Earlier this month, Qihoo 360’s Network Security
Research Lab (360 Netlab) detailed a rapidly spreading DDoS botnet
called Fodcha[7]
that has spread through different N-Day flaws and weak Telnet/SSH
passwords.
One crucial aspect sets Lillin Scanner apart from BotenaGo is
its reliance on an external program to build an IP address list of
vulnerable Lilin devices, subsequently exploiting the
aforementioned flaw to execute arbitrary code remotely on the
target and deploy Mirai payloads.
It’s worth noting that the malware cannot propagate itself in a
worm-like fashion, and can only be used to strike the IP addresses
provided as input with the Mirai binaries.
“Another behavior associated with the Mirai botnet is the
exclusion of IP ranges belonging to the internal networks of the
U.S. Department of Defense (DoD), U.S. Postal Service (USPS),
General Electric (GE), Hewlett-Packard (HP), and others,” the
researchers said.
Like Mirai, the emergence of Lilin Scanner points to the reuse
of readily available source code to spawn new malware
offshoots.
“Its authors removed almost all of the 30+ exploits present in
BotenaGo’s original source code,” the researchers said, adding, “it
seems that this tool has been quickly built using the code base of
the BotenaGo malware.”
References
- ^
Lilin
Scanner (www.nozominetworks.com) - ^
latest
version (www.virustotal.com) - ^
command
injection vulnerability
(www.meritlilin.com) - ^
BotenaGo
(thehackernews.com) - ^
said
(thehackernews.com) - ^
latest
(blog.netlab.360.com) - ^
Fodcha
(thehackernews.com)
Read more https://thehackernews.com/2022/04/new-botenago-malware-variant-targeting.html