Security researchers have disclosed a security vulnerability
that could allow an attacker to weaponize the VirusTotal platform
as a conduit to achieve remote code execution (RCE) on unpatched
third-party antivirus engines.
The flaw, now patched, made it possible to “execute commands
remotely within VirusTotal platform and gain access to its various
scans capabilities,” Cysource researchers Shai Alfasi and Marlon
Fabiano da Silva said in a report[1]
exclusively shared with The Hacker News.
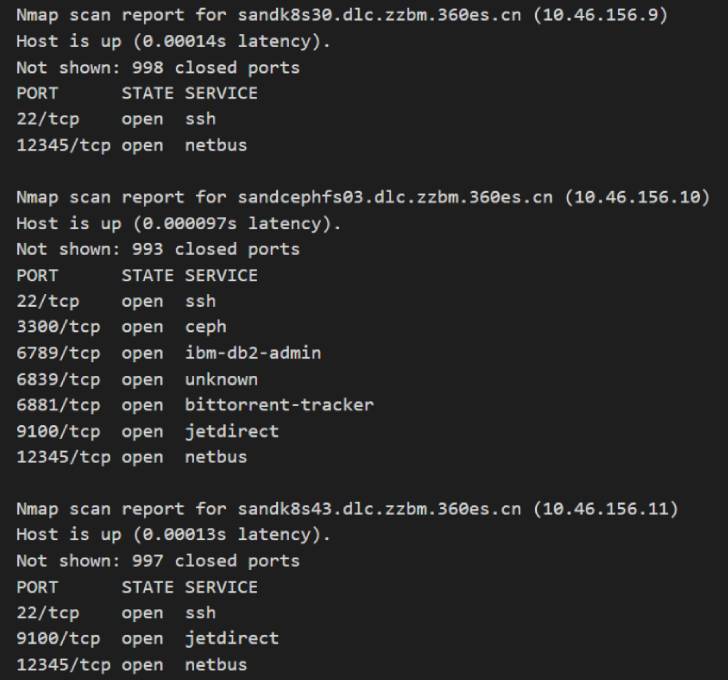
VirusTotal[2], part of Google’s
Chronicle security subsidiary, is a malware-scanning service that
analyzes suspicious files and URLs and checks for viruses using
more than 70 third-party antivirus products.
The attack method involved the upload of a DjVu file through the
platform’s web user interface[3], using it to trigger an
exploit for a high-severity remote code execution flaw in ExifTool[4], an open-source utility
used to read and edit EXIF metadata information in image and PDF
files.
Tracked as CVE-2021-22204[5]
(CVSS score: 7.8), the high-severity vulnerability[6]
in question is a case of arbitrary code execution that arises from
ExifTool’s mishandling of DjVu files. The issue was patched by its
maintainers in a security
update[7] released on April 13,
2021.
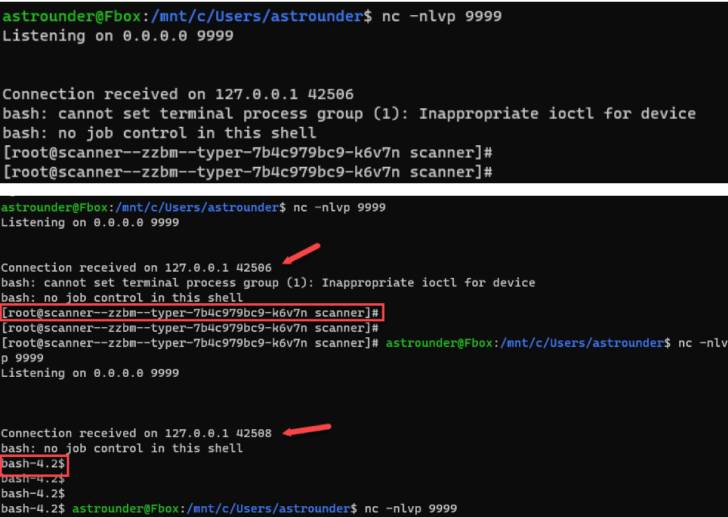
A consequence of such an exploitation, the researchers noted,
was that it granted a reverse shell to affected antivirus engines
that had not yet been patched for the remote code execution
vulnerability.
In a statement shared with The Hacker News, VirusTotal confirmed
that it’s the intended behavior and that the code executions are
not in the platform itself but in the third-party scanning systems
that analyze and execute the samples. The company also said it’s
using a version of ExifTool that’s not vulnerable to the flaw.
Cysource said it responsibly reported the bug through Google’s
Vulnerability Reward Programs (VRP[8]) on April 30, 2021,
following which the security weakness was immediately
rectified.
This is not the first time the ExifTool flaw emerged as a
conduit to achieve remote code execution. Last year, GitLab fixed a
critical flaw (CVE-2021-22205[9], CVSS score: 10.0)
related to an improper validation of user-provided images, leading
to arbitrary code execution.
(Update: The story has been revised based on a
statement from VirusTotal to clarify the nature of the
exploitation.)
References
- ^
report
(www.cysrc.com) - ^
VirusTotal
(support.virustotal.com) - ^
web user
interface (www.virustotal.com) - ^
ExifTool
(en.wikipedia.org) - ^
CVE-2021-22204
(nvd.nist.gov) - ^
vulnerability
(devcraft.io) - ^
security
update (exiftool.org) - ^
VRP
(security.googleblog.com) - ^
CVE-2021-22205
(thehackernews.com)
Read more https://thehackernews.com/2022/04/researchers-report-critical-rce.html