TL;DR:
Adopt a modern, test-driven methodology for securing your
organization with Detection-as-Code.
Over the past decade, threat detection has become
business-critical and even more complicated. As businesses move to
the cloud, manual threat detection processes are no longer able to
keep up. How can teams automate security analysis at scale and
address the challenges that threaten business objectives? The
answer lies in treating threat detections like software or
detection-as-code.
Watch Panther’s On-Demand Webinar: Scaling
Security with Detection-as-Code with Cedar[1]
to find out how Cedar uses Panther to leverage Detection-as-Code to
build high-signal alerts.
Detection-as-Code: A New (Hope) Paradigm Detections define logic
for analyzing security log data to identify attacker behaviors.
When a rule is matched, an alert gets sent to your team for
containment or investigation.
What is detection-as-code?
Detection-as-Code is a modern, flexible, and structured approach
to writing detections that apply software engineering best
practices to security. By adopting this new paradigm, teams can
build scalable processes for writing and hardening detections to
identify sophisticated threats across rapidly expanding
environments.
Benefits of Adopting a Code-Driven
Workflow
Threat detection programs that are fine-tuned for specific
environments and systems are the most impactful. By treating
detections as well-written code that can be tested, checked into
source control, and code-reviewed by peers, teams can produce
higher-quality alerts that reduce fatigue and quickly flag
suspicious activity.
1 — Build Custom, Flexible Detections with a Programming
Language
Writing detections in a universally-recognized, flexible, and
expressive language such as Python offers several advantages
instead of using domain-specific languages (DSL) that are too
limited. With languages, such as Python, you can write more
sophisticated and tailored detections to fit the needs specific to
your enterprise. These rules also tend to be more readable and easy
to understand as the complexity increases.
Another benefit of this approach is utilizing a rich set of
built-in or third-party libraries developed by the security
community for interacting with APIs or processing data, which
increases the effectiveness of the detection.
2 — Test-Driven Development (TDD)
A proper QA for detection code can enable teams to discover
detection blind-spots early on, cover testing for false alerts, and
promote detection efficacy. A TDD approach allows security teams to
think like an attacker, document that knowledge, and curate an
internal repository of insight into the attacker’s lifecycle.
The advantage of TDD is more than just validation of code
correctness. A TDD approach to writing detections improves the
quality of detection code and enables more modular, extensible, and
flexible detections. Engineers can easily make changes to their
detection without fear of breaking alerts or hamstringing everyday
operations.
3 — Collaboration with Version
Control Systems
When writing new detections or modifying them, version control
allows teams to quickly and easily revert to previous states. It
also confirms that teams are using the most up-to-date detection
rather than referencing outdated or wrong code. Version control can
also help give needed context for specific detections that
triggered an alert or help pinpoint when detections are
changed.
As new and additional data enters the system over time,
detections must also change. A change control process is essential
to help teams address and adjust the detections as needed, while
simultaneously ensuring that all changes are well-documented and
well-reviewed.
4 — Automated Workflows for
Reliable Detections
A Continuous Integration/Continuous Deployment (CI/CD) pipeline
can be beneficial for security teams that have long wanted to move
security further left. Using a CI/CD pipeline helps achieve the
following two goals:
- Eliminate silos between teams as they work together on a common
platform, code-review each other’s work, and stay organized.
- Provide automated testing and delivery pipelines for your
security detections. Teams can stay agile by focusing on building
fine-tuned detections. Instead of manually testing, deploying, and
ensuring that the detections aren’t overly tuned, which could
trigger false alerts.
5 — Reusable Code
Last but not least, Detection-as-Code can promote code
reusability across a large set of detections. As teams write large
numbers of detections over time, they start to see specific
patterns emerge. Engineers can reuse the existing code to perform
the same or very similar function across different detections
without starting from scratch.
Code reusability can be a vital part of detection-writing that
allows teams to share functions between detections or modify and
adapt detections for specific use-cases. For example, suppose you
needed to repeat a set of Allow/Deny lists (let’s say for access
management) or a particular processing logic in multiple places. In
that case, you can use Helpers in languages such as Python to share
functions between detections.
Introduction to Panther[2]
Panther is a security analytics platform designed to alleviate
the problems of traditional SIEMs. Panther is built for security
engineers, by security engineers. Rather than inventing yet another
proprietary language for expressing detection logic, Panther offers
security teams a Python rules-engine to write expressive threat
detection and automate detection and response at cloud-scale.
Panther’s modular and open approach offers easy integrations and
flexible detections to help you build a modern security operations
pipeline.
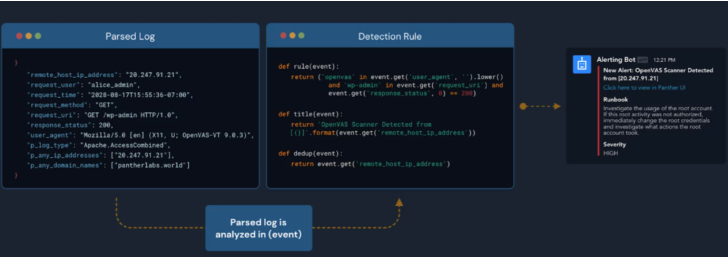 |
| Detection-as-Code workflow in Panther |
Panther[3]
offers reliable and resilient detections that can make it easy
to:
- Write expressive and flexible detections in Python for needs
specific to your enterprise. - Structure and normalize logs into a strict schema that enables
detections with Python and queries with SQL. - Perform real-time threat detection and power investigations
against massive volumes of security data. - Benefit from 200+ pre-built detections mapped to specific
threats, suspicious activity, and security frameworks like MITRE
ATT&CK.
Detection-as-Code workflow in Panther
An Example Detection in Panther
When writing a detection in Panther[4], you start with a rule()
function that identifies a specific behavior to identify. For
example, let’s suppose you want an alert when a brute force Okta
login is suspected. The following detection can help identify this
behavior with Panther:
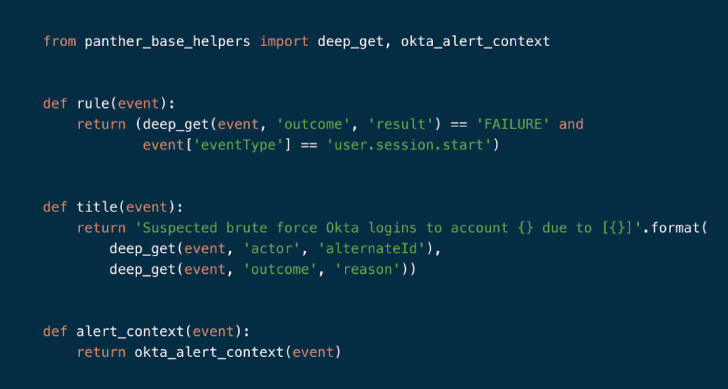 |
| Okta Brute Force Login Rule in Panther |
In the above example:
- The rule() function takes one argument of ‘event’ and returns a
boolean value. - The title() function controls the generated alert message sent
to analysts. Values from the events can then be interpolated to add
helpful contexts.
Rules can be enabled and tested directly in the Panther UI, or
modified and uploaded programmatically with the Panther Analysis
tool, which enables you to test, package, and deploy detections via
the command-line interface (CLI). And to assist with incident
triage, Panther rules contain metadata such as severity, log types,
unit tests, runbooks, and more.
Get Started
Are you taking full advantage of all your security data to
detect threats and suspicious activity? Learn how to secure your
cloud, network, applications, and endpoints with Panther
Enterprise. Request a demo today.[5]
References
- ^
Watch
Panther’s On-Demand Webinar: Scaling Security with
Detection-as-Code with Cedar (panther.com) - ^
Panther
(panther.com) - ^
Panther
(panther.com) - ^
Panther
(panther.com) - ^
Request
a demo today. (panther.com)
Read more https://thehackernews.com/2022/05/5-benefits-of-detection-as-code.html
