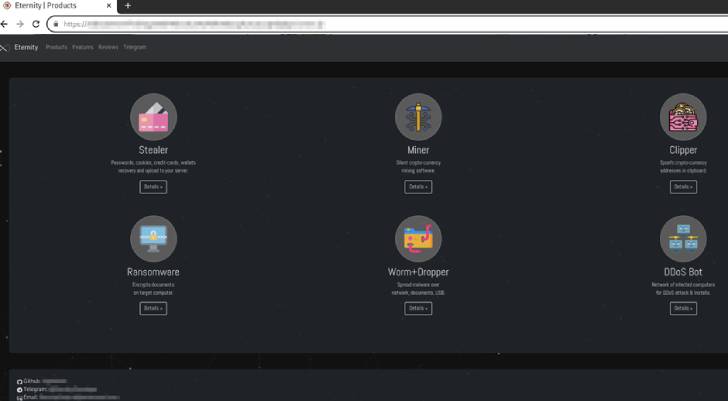
An unidentified threat actor has been linked to an actively
in-development malware toolkit called the “Eternity Project” that
lets professional and amateur cybercriminals buy stealers,
clippers, worms, miners, ransomware, and a distributed
denial-of-service (DDoS) bot.
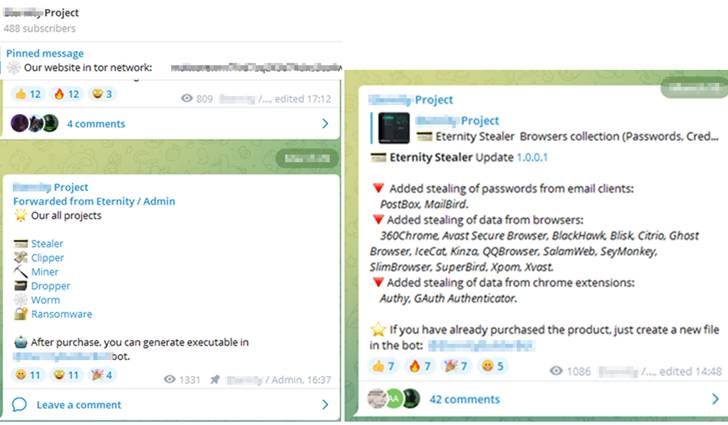
What makes this malware-as-a-service (MaaS) stand out is that
besides using a Telegram channel to communicate updates about the
latest features, it also employs a Telegram Bot[1] that enables the
purchasers to build the binary.
“The [threat actors] provide an option in the Telegram channel
to customize the binary features, which provides an effective way
to build binaries without any dependencies,” researchers from Cyble
said[2]
in a report published last week.
Each of the modules can be leased separately and provides paid
access to a wide variety of functions –
- Eternity Stealer ($260 for an annual subscription) –
Siphon passwords, cookies, credit cards, browser cryptocurrency
extensions, crypto wallets, VPN clients, and email apps from a
victim’s machine and sends them to the Telegram Bot
- Eternity Miner ($90 as an annual subscription) – Abuse
the computing resources of a compromised machine to mine
cryptocurrency
- Eternity Clipper ($110) – A crypto-clipping program that
steals cryptocurrency during a transaction by substituting the
original wallet address saved in the clipboard with the attacker’s
wallet address.
- Eternity Ransomware ($490) – A 130kb ransomware
executable to encrypt all of the users’ files until a ransom is
paid
- Eternity Worm ($390) – A malware that propagates through
USB Drives, local network shares, local files as well as via spam
messages broadcasted on Discord and Telegram.
- Eternity DDoS Bot (N/A) – The feature is said to be
currently under development.
Cyble pointed out there are indications that the malware authors
may be repurposing existing code related to DynamicStealer[3], which is available on
GitHub, and trading it under a new moniker for profit.
It’s worth noting that Jester Stealer, another malware that came
to light in February 2022 and has since been put to use in phishing attacks against Ukraine[4], also utilizes the same
GitHub repository for downloading TOR proxies, indicating possible
links between the two threat actors.
The cybersecurity firm also said it “has observed a significant
increase in cybercrime through Telegram channels and cybercrime
forums where [threat actors] sell their products without any
regulation.”
Just last week, BlackBerry exposed the inner workings of a
remote access trojan called[5]
DCRat (aka DarkCrystal RAT) that’s available for sale at cheap
prices on Russian hacking forums and uses a Telegram channel for
sharing details regarding software and plugin updates.
References
- ^
Telegram Bot
(core.telegram.org) - ^
said
(blog.cyble.com) - ^
DynamicStealer
(github.com) - ^
phishing
attacks against Ukraine (thehackernews.com) - ^
called
(thehackernews.com)
Read more https://thehackernews.com/2022/05/researchers-warn-of-eternity-project.html