Fronton, a distributed denial-of-service (DDoS) botnet that came
to light in March 2020, is much more powerful than previously
thought, per the latest research.
“Fronton is a system developed for coordinated inauthentic
behavior on a massive scale,” threat intelligence firm Nisos said
in a report[1]
published last week.
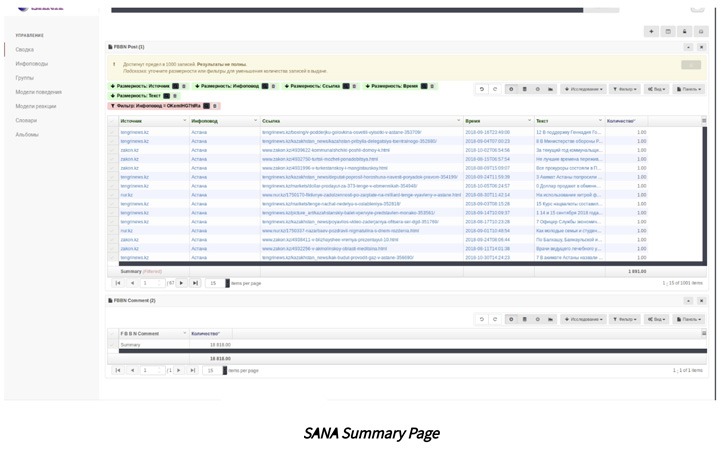
“This system includes a web-based dashboard known as SANA that
enables a user to formulate and deploy trending social media events
en masse. The system creates these events that it refers to as
Инфоповоды, ‘newsbreaks,’ utilizing the botnet as a geographically
distributed transport.”
The existence of Fronton, an IoT botnet, became public knowledge
following revelations from BBC
Russia[2] and ZDNet[3]
in March 2020 after a Russian hacker group known as Digital
Revolution published documents that it claimed were obtained after
breaking into a subcontractor to the FSB, the Federal Security
Service of the Russian Federation.
Further investigation has traced the analytical system to a
Moscow-based company known as Zeroday Technologies (aka 0Dt), with
links identified to a Russian hacker by the name of Pavel Sitnikov[4], who was arrested in
March 2021 on charges of distributing malicious software via his
Telegram channel.
Fronton functions as the backend infrastructure of the social
media disinformation platform, offering an army of compromised IoT
devices for staging DDoS attacks and information campaigns by
communicating with a front-end server infrastructure over VPNs or
the Tor anonymity network.
SANA, on the other hand, is designed to create fake social media
persona accounts and manufacture newsbreaks, which refer to events
that create information “noise” with the goal of shaping online
discourse by means of a response model that allows the bots to
react to the news in a “positive, negative, or neutral
fashion.”
What’s more, the platform enables the operators to control the
amount of likes, comments, and reactions a bot account can create
as well as specify a numeric range of the number of friends such
accounts should maintain. It also incorporates an “Albums” feature
to store imagery for the bot accounts.
It’s not immediately clear if the tool was ever used in
real-world attacks, whether be it by the FSB or otherwise.
The findings come as Meta Platforms said[5]
it took steps against covert adversarial networks originating from
Azerbaijan and Iran on its platform, by taking down the accounts
and blocking their domains from being shared.
Cybersecurity company Mandiant, in an independent report
published last week, revealed that actors aligned with
nation-states such as Russia, Belarus, China, and Iran have mounted
“concerted information operations” in the aftermath of Russia’s
full-scale invasion of Ukraine.
“Russia-aligned operations, including those attributed to
Russian, Belarusian, and pro-Russia actors, have thus far employed
the widest array of tactics, techniques, and procedures (TTPs) to
support tactical and strategic objectives, directly linked to the
conflict itself,” Mandiant noted[6].
“Meanwhile, pro-PRC and pro-Iran campaigns have leveraged the
Russian invasion opportunistically to further progress long-held
strategic objectives.”
References
Read more https://thehackernews.com/2022/05/fronton-russian-iot-botnet-designed-to.html