|
| Image Source: Toptal |
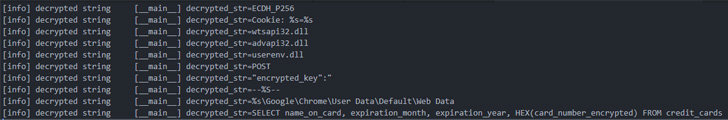
The notorious Emotet malware has turned to deploy a new module
designed to siphon credit card information stored in the Chrome web
browser.
The credit card stealer, which exclusively singles out Chrome,
has the ability to exfiltrate the collected information to
different remote command-and-control (C2) servers, according to
enterprise security company Proofpoint[1], which observed the
component on June 6.
The development comes amid a spike[2]
in Emotet[3]
activity[4]
since it was resurrected late last year following a 10-month-long
hiatus in the wake of a law enforcement operation that took down its attack
infrastructure[5]
in January 2021.
Emotet, attributed to a threat actor known as TA542 (aka Mummy
Spider or Gold Crestwood), is an advanced, self-propagating and
modular trojan that’s delivered via email campaigns and is used as
a distributor for other payloads such as ransomware.
As of April 2022, Emotet is still the most popular malware with
a global impact of 6% of organizations worldwide, followed by
Formbook[6]
and Agent Tesla[7], per Check Point[8], with the malware
testing out new delivery methods using OneDrive URLs[9]
and PowerShell in .LNK attachments[10] to get around
Microsoft’s macro restrictions[11].
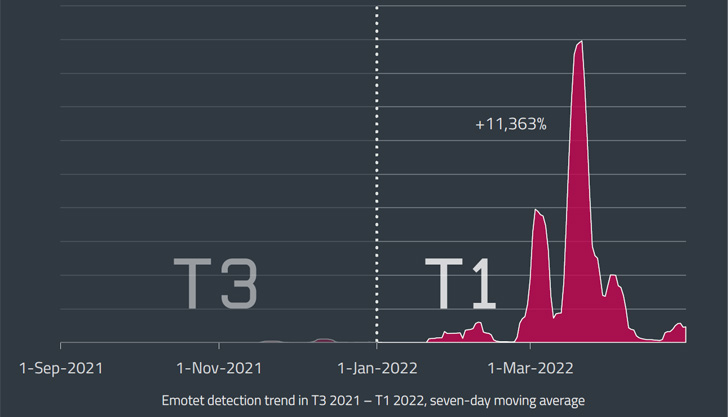
The steady growth[12] in Emotet-related
threats is substantiated further by the fact that the number of
phishing emails, often hijacking already existing correspondence,
grew from 3,000 in February 2022 to approximately 30,000 in March
targeting organizations in various countries as part of a
mass-scale spam campaign.
Stating that Emotet activity have “shifted to a higher gear” in
March and April 2022, ESET said that detections jumped a 100-fold,
registering a growth of over 11,000% during the first four months
of the year when compared to the preceding three-month period from
September to December 2021.
Some of the common targets since the botnet’s resurrection have
been Japan, Italy, and Mexico, the Slovak cybersecurity company
noted, adding the biggest wave was recorded on March 16, 2022.
“The size of Emotet’s latest LNK and XLL campaigns was
significantly smaller than those distributed via compromised DOC
files seen in March,” Dušan Lacika, senior detection engineer at
Dušan Lacika, said[13].
“This suggests that the operators are only using a fraction of
the botnet’s potential while testing new distribution vectors that
could replace the now disabled-by-default VBA macros.”
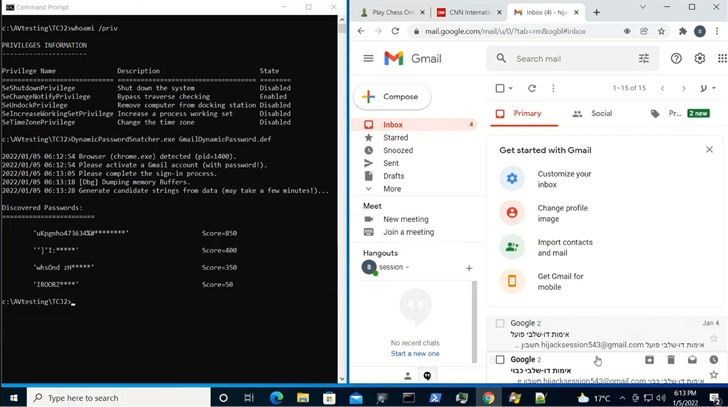
The findings also come as researchers from CyberArk demonstrated
a new technique[14] to extract plaintext
credentials directly from memory in Chromium-based web
browsers.
“Credential data is stored in Chrome’s memory in cleartext
format,” CyberArk’s Zeev Ben Porat said[15]. “In addition to data
that is dynamically entered when signing into specific web
applications, an attacker can cause the browser to load into memory
all the passwords that are stored in the password manager.”
This also includes cookie-related information such as session
cookies, potentially allowing an attacker to extract the
information and use it to hijack users’ accounts even when they are
protected by multi-factor authentication.
References
- ^
Proofpoint
(twitter.com) - ^
spike
(thehackernews.com) - ^
Emotet
(thehackernews.com) - ^
activity
(thehackernews.com) - ^
took
down its attack infrastructure
(thehackernews.com) - ^
Formbook
(thehackernews.com) - ^
Agent
Tesla (malpedia.caad.fkie.fraunhofer.de) - ^
Check
Point (www.checkpoint.com) - ^
OneDrive
URLs (thehackernews.com) - ^
PowerShell in .LNK attachments
(twitter.com) - ^
macro
restrictions (thehackernews.com) - ^
steady
growth (usa.kaspersky.com) - ^
said
(www.welivesecurity.com) - ^
technique
(bugs.chromium.org) - ^
said
(www.cyberark.com)
Read more https://thehackernews.com/2022/06/new-emotet-variant-stealing-users.html