Researchers have disclosed what they say could be an attempt to
kick-off a new large-scale cryptocurrency mining campaign targeting
the NPM JavaScript package repository.
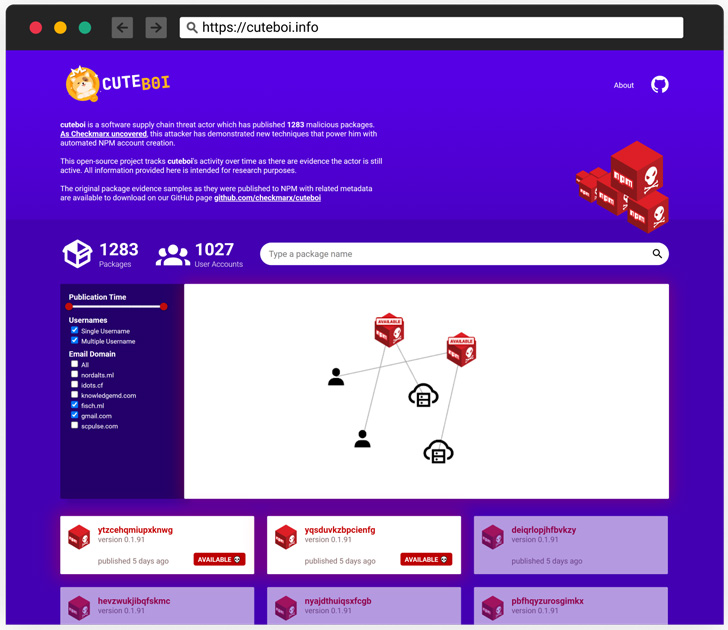
The malicious activity, attributed to a software supply chain
threat actor dubbed CuteBoi[1], involves an array of
1,283 rogue modules that were published in an automated fashion
from over 1,000 different user accounts.
“This was done using automation which includes the ability to
pass the NPM 2FA challenge,” Israeli application security testing
company Checkmarx said[2]. “This cluster of
packages seems to be a part of an attacker experimenting at this
point.”
All the released packages in question are said to harbor
near-identical source code from an already existing package named
eazyminer that’s used to mine Monero by means of utilizing unused
resources on web servers.
One notable modification entails the URL to which the mined
cryptocurrency should be sent, although installing the rogue
modules will not bring about a negative effect.
“The copied code from eazyminer[3]
includes a miner functionality intended to be triggered from within
another program and not as a standalone tool,” researcher Aviad
Gershon said. “The attacker didn’t change this feature of the code
and for that reason, it won’t run upon installation.”
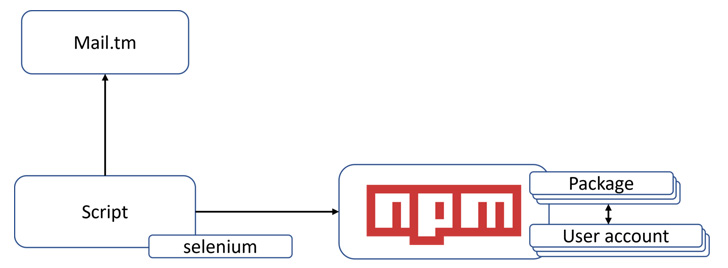
Like observed in the case of RED-LILI[4]
earlier this year, the packages are published via an automation
technique that allows the threat actor to defeat two-factor
authentication (2FA) protections.
However, while the former involved setting up a custom server
and using a combination of tools like Selenium and Interactsh to
programmatically create an NPM user account and defeat 2FA, CuteBoi
relies on a disposable email service called mail.tm[5].
Specifically, it employs a REST API[6] offered by the free
platform that enables “programs to open disposable mailboxes and
read the received emails sent to them with a simple API call.” This
allows the threat actor to circumvent 2FA when creating a flood of
user accounts to publish the packages.
The findings coincide with another NPM-related widespread
software supply chain attack dubbed IconBurst[7]
that’s engineered to harvest sensitive data from forms embedded in
downstream mobile applications and websites.
References
Read more https://thehackernews.com/2022/07/over-1200-npm-packages-found-involved.html