A malicious browser extension with 350 variants is masquerading
as a Google Translate add-on as part of an adware campaign
targeting Russian users of Google Chrome, Opera, and Mozilla
Firefox browsers.
Mobile security firm Zimperium dubbed the malware family
ABCsoup, stating the “extensions are installed
onto a victim’s machine via a Windows-based executable, bypassing
most endpoint security solutions, along with the security controls
found in the official extension stores.”
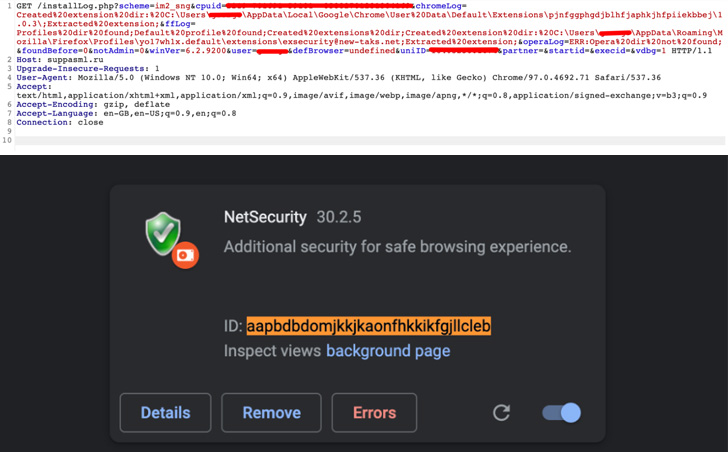
The rogue browser add-ons come with the same extension ID as
that of Google Translate — “aapbdbdomjkkjkaonfhkkikfgjllcleb[1]” — in an attempt to
trick users into believing that they have installed a legitimate
extension.
The extensions are not available on the official browser web
stores themselves. Rather they are delivered through different
Windows executables that install the add-on on the victim’s web
browser.
In the event the targeted user already has the Google Translate
extension installed, it replaces the original version with the
malicious variant owing to their higher version numbers (30.2.5 vs.
2.0.10).
“Furthermore, when this extension is installed, Chrome Web Store
assumes that it is Google Translate and not the malicious extension
since the Web Store only checks for extension IDs,” Zimperium
researcher Nipun Gupta said[2].
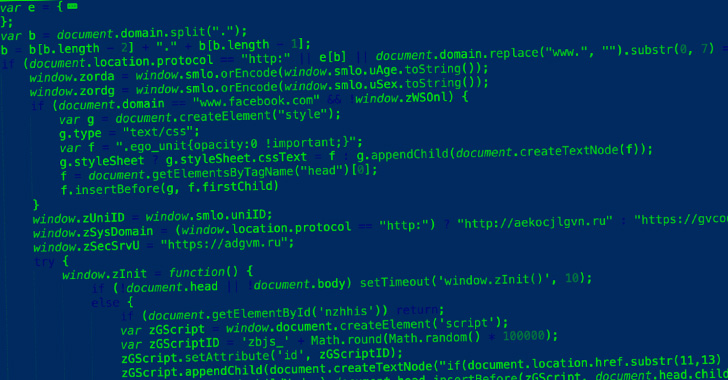
All the observed variants of the extension are geared towards
serving pop-ups, harvesting personal information to deliver
target-specific ads, fingerprinting searches, and injecting
malicious JavaScript that can further act as a spyware to capture
keystrokes and monitor web browser activity.
The main function of ABCsoup entails checking for Russian social
networking services like Odnoklassniki and VK among the current
websites opened in the browser, and if so, gather the users’ first
and last names, dates of birth, and gender, and transmit the data
to a remote server.
Not only does the malware use this information to serve
personalized ads, the extension also comes with capabilities to
inject custom JavaScript code based on the websites opened. This
includes YouTube, Facebook, ASKfm, Mail.ru, Yandex, Rambler, Avito,
Brainly’s Znanija, Kismia, and rollApp, suggesting a heavy Russia
focus.
Zimperium attributed the campaign to a “well-organized group” of
Eastern European and Russian origin, with the extensions designed
to target Russian users given the wide variety of local domains
targeted.
“This malware is purposefully designed to target all kinds of
users and serves its purpose of retrieving user information,” Gupta
said. “The injected scripts can be easily used to serve more
malicious behavior into the browser session, such as keystroke
mapping and data exfiltration.”
References
- ^
aapbdbdomjkkjkaonfhkkikfgjllcleb
(chrome.google.com) - ^
said
(blog.zimperium.com)
Read more https://thehackernews.com/2022/07/experts-uncover-350-browser-extension.html