With speculative execution attacks remaining a stubbornly
persistent vulnerability ailing modern processors, new research has
highlighted an “industry failure” to adopting mitigations released
by AMD and Intel, posing a firmware supply chain threat.
Dubbed FirmwareBleed by Binarly, the
information leaking assaults stem from the continued exposure of
microarchitectural attack surfaces on the part of enterprise
vendors either as a result of not correctly incorporating the fixes
or only using them partially.
“The impact of such attacks is focused on disclosing the content
from privileged memory (including protected by virtualization
technologies) to obtain sensitive data from processes running on
the same processor (CPU),” the firmware protection firm said[1]
in a report shared with The Hacker News.
“Cloud environments can have a greater impact when a physical
server can be shared by multiple users or legal entities.”
In recent years, implementations of speculative execution, an
optimization technique[2]
that predicts the outcome and target of branch instructions in a
program’s execution pipeline, have been deemed susceptible to
Spectre[3]-like attacks on
processor architectures, potentially enabling a threat actor to
leak cryptographic keys and other secrets.
This works by tricking the CPU into executing an instruction
that accesses sensitive data in memory that would normally be
off-limits to an unprivileged application and then extracting the
data after the operation is undone following a misprediction.
A key countermeasure to prevent the harmful effects of
speculative execution is a software defense known as retpoline[4]
(aka “Return Trampoline”), which was introduced in 2018.
Although recent findings such as Retbleed[5]
have conclusively shown that retpoline by itself is insufficient
against stopping such attacks in certain scenarios, the latest analysis[6]
shows a lack of consistency in even applying these mitigations in
the first place.
Specifically, it takes aim at a best practice called Return
Stack Buffer (RSB[7]) stuffing introduced by
Intel to avoid[8]
underflows[9]
when using retpoline. RSBs are address predictors for return (aka
RET) instructions.
“Certain processors may use branch predictors other than the
Return Stack Buffer (RSB) when the RSB underflows,” Intel notes[10] in its documentation.
“This might impact software using the retpoline mitigation strategy
on such processors.”
“On processors with different empty RSB behavior, [System
Management Mode] code should stuff the RSB with CALL instructions
before returning from SMM to avoid interfering with non-SMM usage
of the retpoline technique.”
Intel is also recommending[11] RSB stuffing as a
mechanism to thwart buffer underflow attacks like Retbleed,
alternatively urging[12] vendors to “set
[Indirect Branch Restricted Speculation] before RET instructions at
risk of underflow due to deep call stacks.”
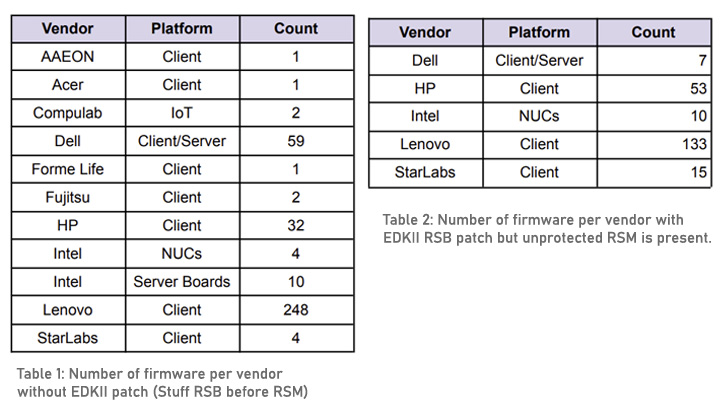
The Binarly research, however, has identified as many as 32
firmware from HP, 59 from Dell, and 248 from Lenovo as having not
included the RSB stuffing patches, underscoring a “failure in the
firmware supply chain.”
What’s more, the deep code analysis has unearthed instances
wherein mitigation was present in the firmware, but contained
implementation mistakes that spawned security issues of its own,
even in updates released in 2022 and for devices featuring the
recent generation of hardware.
“Firmware supply chain ecosystems are quite complex and often
contain repeatable failures when it comes to applying new
industry-wide mitigations or fixing reference code
vulnerabilities,” the researchers said. “Even if a mitigation is
present in the firmware, it doesn’t mean it is applied correctly
without creating security holes.”
References
- ^
said
(binarly.io) - ^
optimization technique
(en.wikipedia.org) - ^
Spectre
(thehackernews.com) - ^
retpoline
(support.google.com) - ^
Retbleed
(thehackernews.com) - ^
latest
analysis (github.com) - ^
RSB (arxiv.org) - ^
avoid
(cwe.mitre.org) - ^
underflows
(developer.apple.com) - ^
notes
(www.intel.com) - ^
recommending
(www.intel.com) - ^
urging
(www.intel.com)
Read more https://thehackernews.com/2022/07/new-study-finds-most-enterprise-vendors.html