More than 1.31 million users attempted to install malicious or
unwanted web browser extensions at least once, new findings from
cybersecurity firm Kaspersky show.
“From January 2020 to June 2022, more than 4.3 million unique
users were attacked by adware hiding in browser extensions, which
is approximately 70% of all users affected by malicious and
unwanted add-ons,” the company said[1].
As many as 1,311,557 users fall under this category in the first
half of 2022, per Kaspersky’s telemetry data. In comparison, the
number of such users peaked in 2020 at 3,660,236, followed by
1,823,263 unique users in 2021.
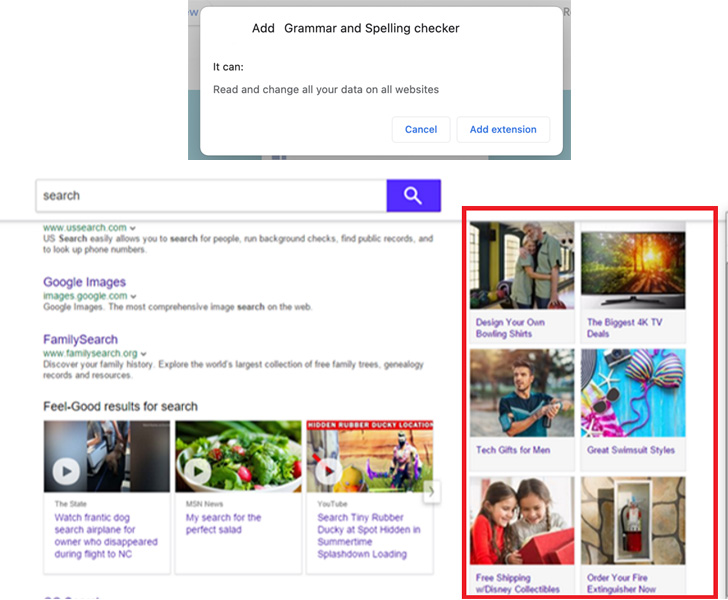
The most prevalent threat is a family of adware called
WebSearch, which masquerade as PDF viewers and other utilities, and
comes with capabilities to collect and analyze search queries and
redirect users to affiliate links.
WebSearch is also notable for modifying the browser’s start
page, which contains a search engine and a number of links to
third-party sources like AliExpress that, when clicked by the
victim, help the extension developers earn money through affiliate
links.
“Also, the extension modifies the browser’s default search
engine to search.myway[.]com, which can capture user queries,
collect and analyze them,” Kaspersky noted. “Depending on what the
user searched for, most relevant partner sites will be actively
promoted in the search results.”
A second set of extensions involve a threat named AddScript that
conceals its malicious functionality under the guise of video
downloaders. While the add-ons do offer the advertised features,
they are also designed to contact a remote server to retrieve and
execute a piece of arbitrary JavaScript code.
Over one million users are said to have encountered adware in H1
2022 alone, with WebSearch and AddScript targeting 876,924 and
156,698 unique users.
Also found were instances of information-stealing malware like
FB Stealer, which aim to steal Facebook login credentials and
session cookies of logged-in users. FB Stealer has been responsible
for 3,077 unique infection attempts in H1 2022.
The malware primarily singles out users on the lookout for
cracked software on search engines, with FB Stealer delivered
through a trojan called NullMixer, which propagates through cracked
installers for software such as SolarWinds Broadband Engineers
Edition.
“FB Stealer is installed by the malware rather than by the
user,” the researchers said. “Once added to the browser, it mimics
the harmless and standard-looking Chrome extension Google
Translate.”
These attacks are also financially-motivated. The malware
operators, after getting hold of the authentication cookies, log in
to the target’s Facebook account and hijack it by changing the
password, effectively locking out the victim. The attackers can
then abuse the access to ask the victim’s friends for money.
The findings come a little over a month after Zimperiumm
disclosed a malware family called ABCsoup[2]
that masquerades as a Google Translate extension as part of an
adware campaign targeting Russian users of Google Chrome, Opera,
and Mozilla Firefox browsers.
To keep the web browser free of infections, it’s recommended
that users stick to trusted sources for downloading software,
review extension permissions, and periodically review and uninstall
add-ons that “you no longer use or that you do not recognize.”
Read more https://thehackernews.com/2022/08/malicious-browser-extensions-targeted.html