The Donot Team threat actor has updated its Jaca
Windows malware toolkit with improved capabilities, including a
revamped stealer module designed to plunder information from Google
Chrome and Mozilla Firefox browsers.
The improvements also include a new infection chain that
incorporates previously undocumented components to the modular
framework, Morphisec researchers Hido Cohen and Arnold Osipov
disclosed[1]
in a report published last week.
Also known as APT-C-35 and Viceroy Tiger, the Donot Team is
known for setting its sights on defense, diplomatic, government,
and military entities in India, Pakistan, Sri Lanka, and
Bangladesh, among others at least since 2016.
Evidence unearthed by Amnesty International in October 2021
connected[2]
the group’s attack infrastructure to an Indian cybersecurity
company called Innefu Labs.
Spear-phishing campaigns containing malicious Microsoft Office
documents are the preferred delivery pathway for malware, followed
by taking advantage of macros and other known vulnerabilities in
the productivity software to launch the backdoor.
The latest findings from Morphisec build on a prior report from
cybersecurity company ESET, which detailed[3]
the adversary’s intrusions against military organizations based in
South Asia using several versions of its yty malware framework, one
of which is Jaca.
This entails the use of RTF documents that trick users into
enabling macros, resulting in the execution of a piece of shellcode
injected into memory that, in turn, is orchestrated to download a
second-stage shellcode from its command-and-control (C2)
server.
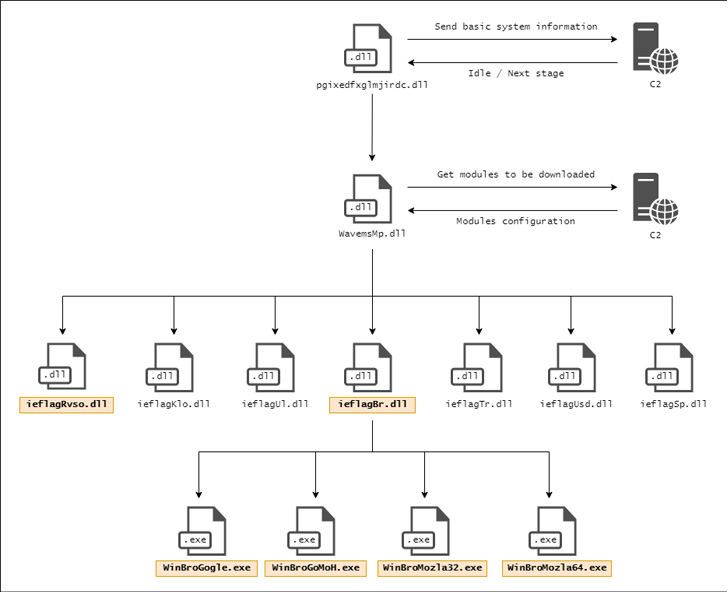
The second-stage then acts as a channel to retrieve a DLL file
(“pgixedfxglmjirdc.dll” from another remote server, which
kick-starts the actual infection by beaconing system information to
the C2 server, establishing persistence via a Scheduled Task, and
fetching the next-stage DLL (“WavemsMp.dll”).
“The main purpose of this stage is to download and execute the
modules used to steal the user’s information,” the researchers
noted. “To understand which modules are used in the current
infection, the malware communicates with another C2 server.”
The C2 domain, for its part, is obtained by accessing an
embedded link that points to a Google Drive document, allowing the
malware to access a configuration that dictates the modules to be
downloaded and executed.
These modules expand on the malware’s features and harvest a
wide range of data such as keystrokes, screenshots, files, and
information stored in web browsers. Also, part of the toolset is a
reverse shell module that grants the actor remote access to the
victim machine.
The development is yet another sign that threat actors are
actively adapting their tactics and techniques that are most
effective in gaining initial infection and maintaining remote
access for extended periods of time.
“Defending against APTs like the Donot team requires a
Defense-in-Depth strategy that uses multiple layers of security to
ensure redundancy if any given layers are breached,” the
researchers said.
References
Read more https://thehackernews.com/2022/08/donot-team-hackers-updated-its-malware.html