Organizations in the Spanish-speaking nations of Mexico and
Spain are in the crosshairs of a new campaign designed to deliver
the Grandoreiro banking trojan.
“In this campaign, the threat actors impersonate government
officials from the Attorney General’s Office of Mexico City and
from the Public Ministry in the form of spear-phishing emails in
order to lure victims to download and execute ‘Grandoreiro,’ a
prolific banking trojan that has been active since at least 2016,
and that specifically targets users in Latin America,” Zscaler
said[1]
in a report.
The ongoing attacks, which commenced in June 2022, have been
observed to target automotive, civil and industrial construction,
logistics, and machinery sectors via multiple infection chains in
Mexico and chemicals manufacturing industries in Spain.
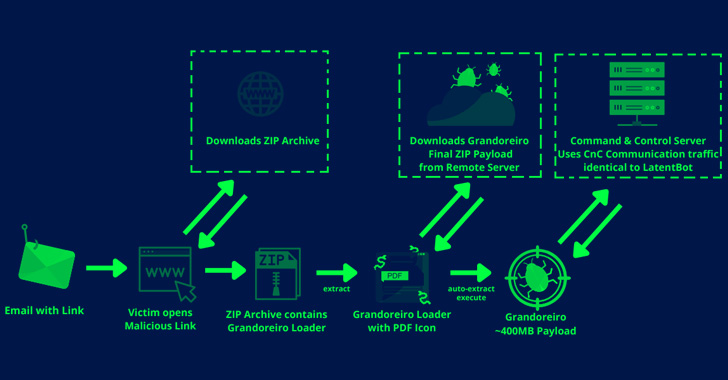
Attack chains entail leveraging spear-phishing emails written in
Spanish to trick potential victims into clicking on an embedded
link that retrieves a ZIP archive, from which is extracted a loader
that masquerades as a PDF document to trigger the execution.
The phishing messages prominently incorporate themes revolving
around payment refunds, litigation notifications, cancellation of
mortgage loans, and deposit vouchers, to activate the
infections.
“This [loader] is responsible for downloading, extracting and
executing the final 400MB ‘Grandoreiro’ payload from a Remote HFS
server which further communicates with the [command-and-control]
Server using traffic identical[2]
to LatentBot[3],” Zscaler researcher
Niraj Shivtarkar said.
That’s not all. The loader is also designed to gather system
information, retrieve a list of installed antivirus solutions,
cryptocurrency wallets, banking, and mail apps, and exfiltrate the
information to a remote server.
Observed in the wild for at least six years, Grandoreiro is a
modular backdoor[4]
with an array of functionalities that allows it to record
keystrokes, execute arbitrary commands, mimic mouse and keyboard
movements, restrict access to specific websites, auto-update
itself, and establish persistence via a Windows Registry
change.
What’s more, the malware is written in Delphi and utilizes
techniques like binary padding to inflate the binary size by 200MB,
CAPTCHA implementation for sandbox evasion, and C2 communication
using subdomains generated via a domain generation algorithm
(DGA[5]).
The CAPTCHA technique[6], in particular, requires
the manual completion of the challenge-response test to execute the
malware in the compromised machine, meaning that the implant is not
run unless and until the CAPTCHA is solved by the victim.
The findings suggest that Grandoreiro is continuously evolving
into a sophisticated malware with novel anti-analysis
characteristics, granting the attackers full remote access
capabilities and posing significant threats to employees and their
organizations.
The development also arrives a little over a year after Spanish
law enforcement agencies apprehended[7]
16 individuals belonging to a criminal network in connection with
operating Mekotio and Grandoreiro in July 2021.
References
- ^
said
(www.zscaler.com) - ^
identical
(seguranca-informatica.pt) - ^
LatentBot
(malpedia.caad.fkie.fraunhofer.de) - ^
modular
backdoor (thehackernews.com) - ^
DGA
(en.wikipedia.org) - ^
CAPTCHA
technique (twitter.com) - ^
apprehended
(thehackernews.com)
Read more https://thehackernews.com/2022/08/new-grandoreiro-banking-malware.html