A security researcher who has a long line of work demonstrating
novel data exfiltration methods from air-gapped systems has come up
with yet another technique that involves sending Morse code signals
via LEDs on network interface cards (NICs[1]).
The approach, codenamed ETHERLED[2], comes from Dr. Mordechai Guri[3], the head of R&D in
the Cyber Security Research Center in the Ben Gurion University of
the Negev in Israel, who recently outlined GAIROSCOPE[4], a method for
transmitting data ultrasonically to smartphone gyroscopes.
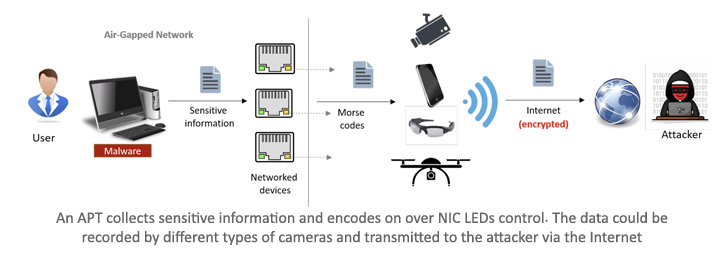
“Malware installed on the device could programmatically control
the status LED by blinking or alternating its colors, using
documented methods or undocumented firmware commands,” Dr. Guri
said.
“Information can be encoded via simple encoding such as Morse
code and modulated over these optical signals. An attacker can
intercept and decode these signals from tens to hundreds of meters
away.”
A network interface card, also known as a network interface
controller or network adapter, is a computer hardware component
that connects a computer to a computer network. LEDs integrated
into the network connector notify the user of whether the network
is connected, and when data activity occurs.
ETHERLED, like other adversarial approaches against air-gapped
systems, requires the intruder to breach the target environment and
plant malicious code that makes it possible to control the NIC
LEDs.
The second phase of the attack relates to data collection and
exfiltration, during which sensitive information is encoded and
sent over an optical covert channel by using the network card’s
status LEDs.
In the final stage, the optical signals are received via a
hidden camera that’s positioned in a location with a direct line of
sight with the compromised transmitting computer. Alternatively,
the camera could also be a surveillance camera that’s vulnerable to
remote exploitation or a smartphone that involves a rogue
insider.
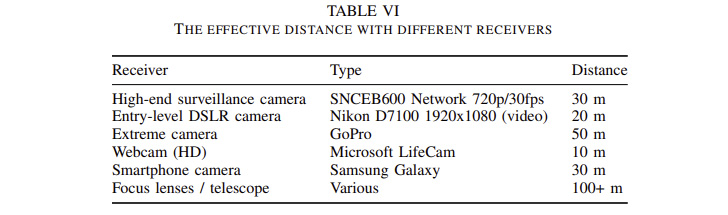
The attack can be used to leak various types of information,
including passwords, RSA encryption keys, keystrokes, and textual
content, to cameras located anywhere between 10m and 50m, a
distance that can be further extended to a few hundred meters by
using a telescope and special focus lenses.
What’s more, the ETHERLED method is designed to work with
peripherals or hardware that are shipped with Ethernet cards, such
as printers, network cameras, network-attached storage (NAS)
devices, embedded systems, and other IoT devices.
Countermeasures include restricting cameras and video recorders
in sensitive zones, covering the status LEDs with black tape to
block the optical emanation physically, reprogramming the software
to defeat the encoding scheme, and jamming the environment to add
random noise to the modulated signals.
References
- ^
NICs
(en.wikipedia.org) - ^
ETHERLED
(arxiv.org) - ^
Dr.
Mordechai Guri (www.linkedin.com) - ^
GAIROSCOPE
(thehackernews.com)
Read more https://thehackernews.com/2022/08/air-gapped-devices-can-send-covert.html