The Python Package Index, PyPI, on Wednesday sounded the alarm
about an ongoing phishing campaign that aims to steal developer
credentials and inject malicious updates to legitimate
packages.
“This is the first known phishing attack against PyPI,” the
maintainers of the official third-party software repository
said[1]
in a series of tweets.
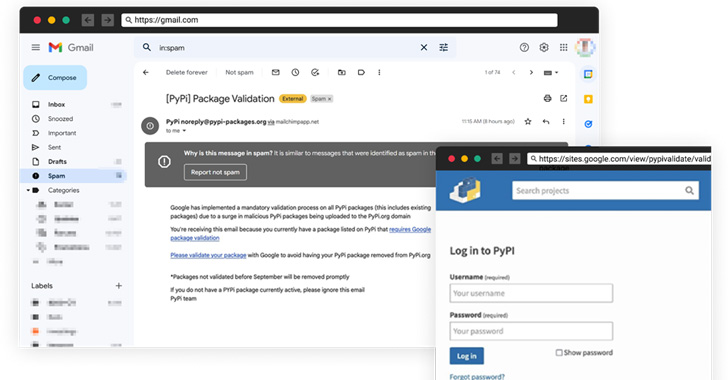
The social engineering attack entails sending security-themed
messages that create a false sense of urgency by informing
recipients that Google is implementing a mandatory validation
process on all packages and that they need to click on a link to
complete the validation before September, or risk getting their
PyPI modules removed.
Should an unsuspecting developer fall for the scheme, users are
directed to a lookalike landing page that mimics PyPI’s login page
and is hosted on Google Sites, from where the entered credentials
are captured and abused to unauthorizedly access the accounts and
compromise the packages to include malware.
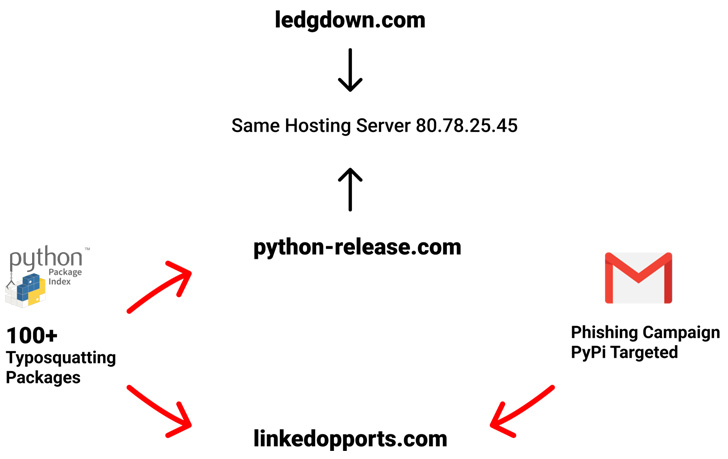
The modifications, for their part, are designed to download a
file from a remote server. “This malware[2]
is untypically large, ~63MB, (possibly in an attempt to evade
[antivirus] detection) and has a valid signature (signed on August
23rd, 2022),” Checkmarx researcher Aviad Gershon noted[3].
“These releases have been removed from PyPI and the maintainer
accounts have been temporarily frozen,” PyPI said. Two of the
affected packages so far include “exotel” and “spam.” Additionally,
several hundred typosquats are said to have been removed.
PyPI also said it’s actively monitoring reports of new rogue
packages and ensuring their removal. Developers who believe they
may have been compromised should reset their passwords with
immediate effect, reset 2FA recovery codes, and review PyPI account
logs for anomalous activity.
The phishing attack is yet another sign of how the open source
ecosystem is increasingly at risk[4]
from threat actors, who are capitalizing on libraries and projects
that are woven into the fabric of several applications to mount
supply chain attacks that can have cascading effects.
Earlier this month, researchers from Checkmarx disclosed[5]
two malicious Python packages – typing-unions and aiogram-types –
that impersonated popular packages typing and aiogram to trick
developers into downloading them and infecting their machines with
Cobalt Strike.
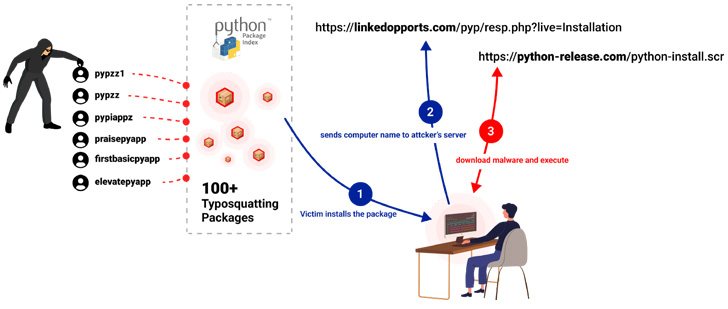
Another large-scale attack involved a threat actor publishing a
dozen typosquatted packages[6] under the names of
popular projects with slight permutations to install a multi-stage
persistent malware on compromised systems.
The development also arrived over two months after the registry
began imposing[7]
a mandatory two-factor authentication (2FA) requirement for
projects deemed “critical.”
References
Read more https://thehackernews.com/2022/08/pypi-repository-warns-python-project.html