An advanced persistent threat (APT) group of Chinese origin
codenamed DiceyF has been linked to a string of
attacks aimed at online casinos in Southeast Asia for years.
Russian cybersecurity company Kaspersky said the activity aligns
with another set of intrusions attributed to Earth Berberoka[1]
(aka GamblingPuppet[2]) and DRBControl[3], citing tactical and
targeting similarities as well as the abuse of secure messaging
clients.
“Possibly we have a mix of espionage and [intellectual property]
theft, but the true motivations remain a mystery,” researchers Kurt
Baumgartner and Georgy Kucherin said[4]
in a technical write-up published this week.
The starting point of the investigation was in November 2021
when Kaspersky said it detected multiple PlugX loaders[5]
and other payloads that were deployed via an employee monitoring
service and a security package deployment service.
The initial infection method – the distribution of the framework
through security solution packages – afforded the threat actor “to
perform cyberespionage activities with some level of stealth,” the
company stated.
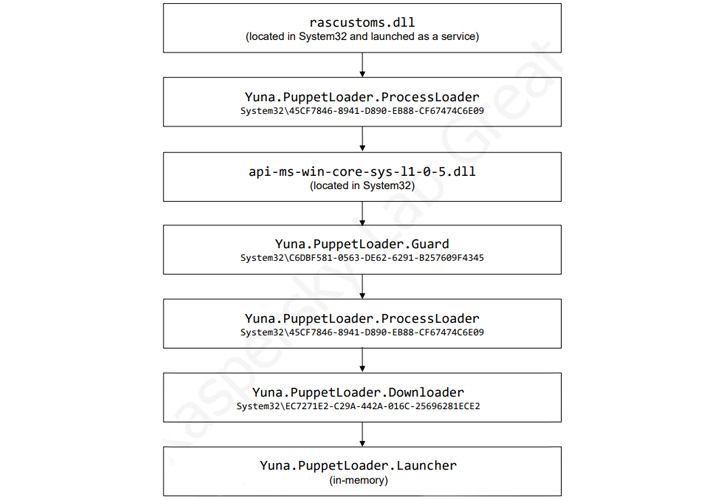
Subsequently, the same security package deployment service is
said to have been employed to deliver what’s called the
GamePlayerFramework, a C# variant of a C++-based malware known as
PuppetLoader.
“This ‘framework’ includes downloaders, launchers, and a set of
plugins that provide remote access and steal keystrokes and
clipboard data,” the researchers explained.
Indications are that the DiceyF activity is a follow-on campaign
to Earth Berberoka with a retooled malware toolset, even as the
framework is maintained through two separate branches dubbed Tifa
and Yuna, which come with different modules of varying levels of
sophistication.
While the Tifa branch contains a downloader and a core
component, Yuna is more complex in terms of functionality,
incorporating a downloader, a set of plugins, and at least 12
PuppetLoader modules. That said, both branches are believed to be
actively and incrementally updated.
Regardless of the variant employed, the GamePlayerFramework,
once launched, connects to a command-and-control (C2) and transmits
information about the compromised host and the clipboard contents,
after which the C2 responds with one of 15 commands that allow the
malware to seize control of the machine.
This also includes launching a plugin on the victim system that
can either be downloaded from the C2 server when the framework is
instantiated or retrieved using the “InstallPlugin” command sent by
the server.
These plugins, in turn, make it possible to steal cookies from
Google Chrome and Mozilla Firefox browsers, capture keystroke and
clipboard data, set up virtual desktop sessions, and even remotely
connect to the machine over SSH.
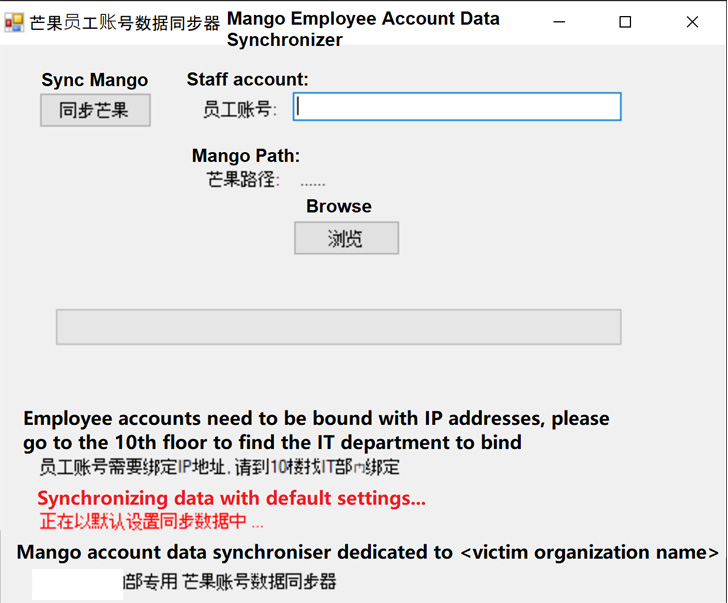
Kaspersky also pointed to the use of a malicious app that mimics
another software called Mango Employee Account Data Synchronizer, a
messenger app used at the targeted entities, to drop the
GamePlayerFramework within the network.
“There are many interesting characteristics of DiceyF campaigns
and TTPs,” the researchers said. “The group modifies their codebase
over time, and develops functionality in the code throughout their
intrusions.”
“To make sure that victims did not become suspicious of the
disguised implants, attackers obtained information about targeted
organizations (such as the floor where the organization’s IT
department is located) and included it inside graphic windows
displayed to victims.”
References
- ^
Earth
Berberoka (thehackernews.com) - ^
GamblingPuppet
(thehackernews.com) - ^
DRBControl
(thehackernews.com) - ^
said
(securelist.com) - ^
PlugX
loaders (thehackernews.com)
Read more https://thehackernews.com/2022/10/chinese-hackers-targeting-online.html