The Ursnif malware has become the latest malware to shed its
roots as a banking trojan to revamp itself into a generic backdoor
capable of delivering next-stage payloads, joining the likes of
Emotet, Qakbot, and TrickBot.
“This is a significant shift from the malware’s original purpose
to enable banking fraud, but is consistent with the broader threat
landscape,” Mandiant researchers Sandor Nemes, Sulian Lebegue, and
Jessa Valdez disclosed[1]
in a Wednesday analysis.
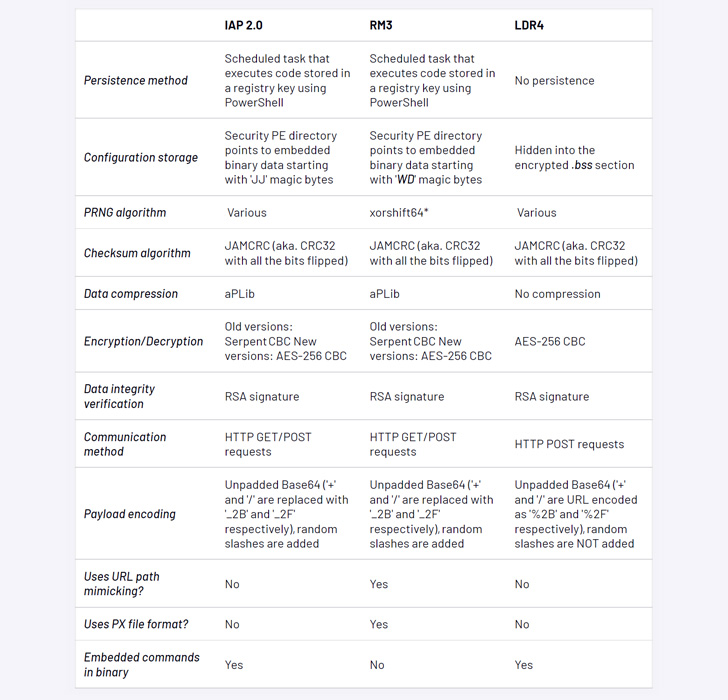
The refreshed and refactored variant, first spotted by the
Google-owned threat intelligence firm in the wild on June 23, 2022,
has been codenamed LDR4, in what’s being seen as an attempt to lay
the groundwork for potential ransomware and data theft extortion
operations.
Ursnif, also called Gozi or ISFB, is one of the oldest banker
malware families, with the earliest
documented attacks[2]
going as far back as 2007. Check Point, in August 2020, mapped the
“divergent evolution of Gozi[3]” over the years, while
pointing out its fragmented development history.
Almost a year later in late June 2021, a Romanian threat actor,
Mihai Ionut Paunescu, was arrested[4]
by Colombian law enforcement officials for his role in propagating
the malware to no fewer than a million computers from 2007 to
2012.
The latest attack chain detailed by Mandiant demonstrates the
use of recruitment and invoice-related email lures as an initial
intrusion vector to download a Microsoft Excel document, which then
fetches and launches the malware.
The major refurbishment of Ursnif eschews all its
banking-related features and modules in favor of retrieving a
VNC module[5]
and gaining a remote shell into the compromised machine, which are
carried out by connecting to a remote server to obtain said
commands.
“These shifts may reflect the threat actors’ increased focus
towards participating in or enabling ransomware operations in the
future,” the researchers said.
References
- ^
disclosed
(www.mandiant.com) - ^
the
earliest documented attacks
(www.secureworks.com) - ^
divergent evolution of Gozi
(research.checkpoint.com) - ^
arrested
(thehackernews.com) - ^
VNC
module (en.wikipedia.org)
Read more https://thehackernews.com/2022/10/latest-ursnif-variant-shifts-focus-from.html