PC maker Lenovo has addressed yet another set of three
shortcomings in the Unified Extensible Firmware Interface (UEFI)
firmware affecting several Yoga, IdeaPad, and ThinkBook
devices.
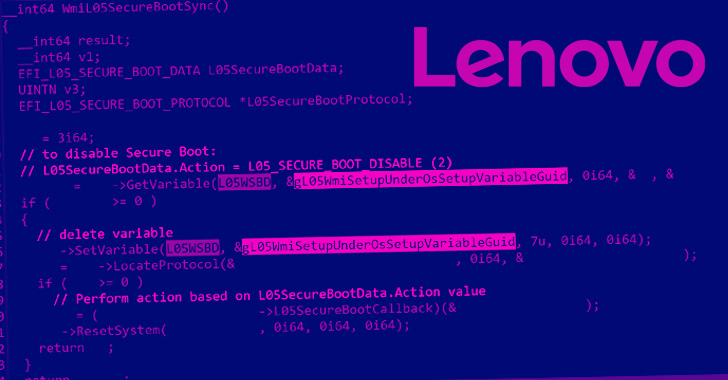
“The vulnerabilities allow disabling UEFI Secure Boot or
restoring factory default Secure Boot databases (incl. dbx): all
simply from an OS,” Slovak cybersecurity firm ESET explained[1]
in a series of tweets.
UEFI refers to software that acts as an interface between the
operating system and the firmware embedded in the device’s
hardware. Because UEFI is responsible[2]
for launching the operating system when a device is powered on, it
has made the technology an attractive option for threat actors
looking to drop malware[3]
that’s difficult to detect and remove.
Viewed in that light, the flaws, tracked as CVE-2022-3430,
CVE-2022-3431, and CVE-2022-3432, could be abused by an adversary
to turn off Secure Boot, a security mechanism that’s designed to
prevent malicious programs from loading during the boot
process.
Lenovo’s advisory describes[4]
the vulnerabilities as follows –
- CVE-2022-3430: A potential vulnerability in
the WMI Setup driver on some consumer Lenovo Notebook devices may
allow an attacker with elevated privileges to modify Secure Boot
setting by modifying an NVRAM variable.
- CVE-2022-3431: A potential vulnerability in a
driver used during the manufacturing process on some consumer
Lenovo Notebook devices that was mistakenly not deactivated may
allow an attacker with elevated privileges to modify Secure Boot
setting by modifying an NVRAM variable.
- CVE-2022-3432: A potential vulnerability in a
driver used during the manufacturing process on the IdeaPad
Y700-14ISK that was mistakenly not deactivated may allow an
attacker with elevated privileges to modify Secure Boot setting by
modifying an NVRAM variable.
In other words, disabling the UEFI Secure Boot makes it possible
for threat actors to execute rogue boot loaders, granting the
attackers privileges access to the compromised hosts.
ESET said the vulnerabilities weren’t lapses in the source code
per se, but rather came into being because the “drivers were meant
to be used only during the manufacturing process but were
mistakenly included in the production.”
The latest update marks the third time Lenovo has moved to patch
flaws in its UEFI firmware, all of which have been discovered and
reported by ESET researcher Martin Smolár.
While the first set of issues (CVE-2021-3970, CVE-2021-3971, and
CVE-2021-3972[5]) could have permitted
bad actors to deploy and execute firmware implants on the affected
devices, the second batch (CVE-2022-1890, CVE-2022-1891, and
CVE-2022-1892[6]) could be weaponized to
achieve arbitrary code execution and disable security features.
Lenovo said it does not intend to release fixes for
CVE-2022-3432 owing to the fact that the model in question has
reached end-of-life (EoL). Users of the other impacted devices are
recommended to update their firmware to the latest version.
References
- ^
explained
(twitter.com) - ^
responsible
(thehackernews.com) - ^
drop
malware (thehackernews.com) - ^
describes
(support.lenovo.com) - ^
CVE-2021-3970, CVE-2021-3971, and
CVE-2021-3972 (thehackernews.com) - ^
CVE-2022-1890, CVE-2022-1891, and
CVE-2022-1892 (thehackernews.com)
Read more https://thehackernews.com/2022/11/new-uefi-firmware-flaws-reported-in.html