A recently discovered cyber espionage group dubbed
Worok has been found hiding malware in seemingly
innocuous image files, corroborating a crucial link in the threat
actor’s infection chain.
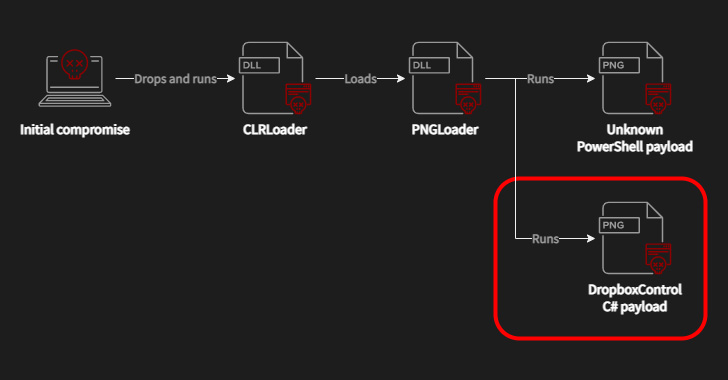
Czech cybersecurity firm Avast said the purpose of the PNG files
is to conceal a payload that’s used to facilitate information
theft.
“What is noteworthy is data collection from victims’ machines
using DropBox repository, as well as attackers using DropBox API
for communication with the final stage,” the company said[1].
The development comes a little over two months after ESET
disclosed details of attacks carried out by Worok[2]
against high-profile companies and local governments located in
Asia and Africa. Worok is believed to share tactical overlaps with
a Chinese threat actor tracked as TA428[3].
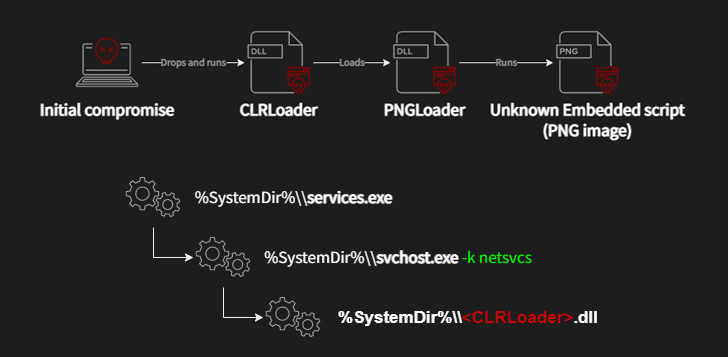
The Slovak cybersecurity company also documented Worok’s
compromise sequence, which makes use of a C++-based loader called
CLRLoad to pave the way for an unknown PowerShell script
embedded within PNG images, a technique known as steganography.
That said, the initial attack vector remains unknown as yet,
although certain intrusions have entailed the use of ProxyShell vulnerabilities[4] in Microsoft Exchange
Server to deploy the malware.
Avast’s findings show that the adversarial collective makes use
of DLL side-loading[5]
upon gaining initial access to execute the CLRLoad malware, but not
before performing lateral movement across the infected
environment.
PNGLoad, which is launched by CLRLoad (or alternatively another
first-stage called PowHeartBeat), is said to come in two variants,
each responsible for decoding the malicious code within the image
to launch either a PowerShell script or a .NET C#-based
payload.
The PowerShell script has continued to be elusive, although
Avast noted it was able to flag a few PNG files belonging to the
second category that dispensed a steganographically embedded C#
malware.
“At first glance, the PNG pictures look innocent, like a fluffy
cloud,” Avast said. “In this specific case, the PNG files are
located in C:\Program Files\Internet Explorer, so the picture does
not attract attention because Internet Explorer has a similar
theme.”
This new malware, dubbed DropBoxControl, is an
information-stealing implant that uses a Dropbox account for
command-and-control, enabling the threat actor to upload and
download files to specific folders as well as run commands present
in a certain file.
Some of the notable commands include the ability to execute
arbitrary executables, download and upload data, delete and rename
files, capture file information, sniff network communications, and
exfiltrate system metadata.
Companies and government institutions in Cambodia, Vietnam, and
Mexico are a few of the prominent countries affected by
DropBoxControl, Avast said, adding the authors of the malware are
likely different from those behind CLRLoad and PNGLoad owing to
“significantly different code quality of these payloads.”
Regardless, the deployment of the third-stage implant as a tool
to harvest files of interest clearly indicates the
intelligence-gathering objectives of Worok, not to mention serves
to illustrate an extension to its killchain.
“The prevalence of Worok’s tools in the wild is low, so it can
indicate that the toolset is an APT project focusing on
high-profile entities in private and public sectors in Asia,
Africa, and North America,” the researchers concluded.
References
- ^
said
(decoded.avast.io) - ^
Worok
(thehackernews.com) - ^
TA428
(thehackernews.com) - ^
ProxyShell vulnerabilities
(thehackernews.com) - ^
DLL
side-loading (attack.mitre.org)
Read more https://thehackernews.com/2022/11/worok-hackers-abuse-dropbox-api-to.html