Dec 07, 2022Ravie Lakshmanan
Cryptocurrency investment companies are the target of a
developing threat cluster that uses Telegram groups to seek out
potential victims.
Microsoft’s Security Threat Intelligence Center (MSTIC) is
tracking the activity under the name DEV-0139, and
builds upon a recent report from Volexity that attributed the same
set of attacks to North Korea’s Lazarus Group[1].
“DEV-0139 joined Telegram groups used to facilitate
communication between VIP clients and cryptocurrency exchange
platforms and identified their target from among the members,” the
tech giant said[2].
The adversary subsequently impersonated another cryptocurrency
investment company and invited the victim to join a different
Telegram chat group under the pretext of asking for feedback on the
trading fee structure used by exchange platforms across VIP
tiers.
It’s worth pointing out that the VIP program[3]
is designed[4]
to reward[5]
high-volume traders[6]
with exclusive trading fee incentives and discounts based on the
activity in the past 30 days.
This attack chain notably dovetails with Volexity’s analysis of
an October 2022 campaign, wherein the threat actor pivoted from
using MSI installer files to a weaponized Microsoft Excel document[7] displaying the supposed
cryptocurrency coin rates.
Microsoft described the document as containing likely accurate
data to increase the likelihood of success of the campaign,
suggesting that DEV-0139 is well versed in the inner workings of
the crypto industry.
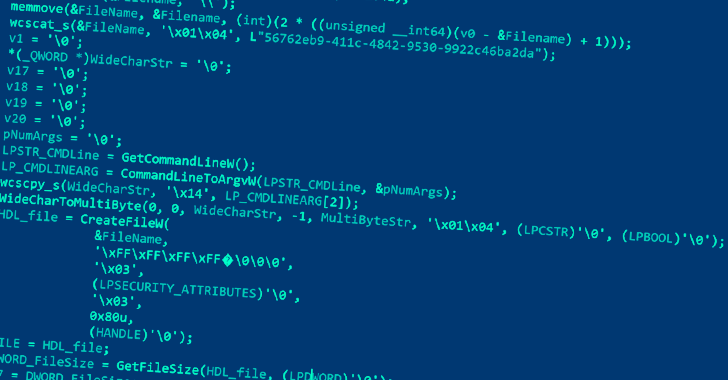
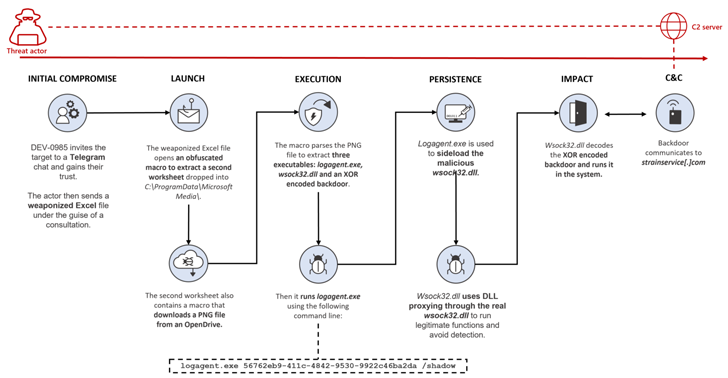
The malware-laced Excel file, for its part, is tasked with
executing a malicious macro that’s used to stealthily drop and
execute a second Excel worksheet, which, in turn, includes a macro
that downloads a PNG image file hosted on OpenDrive.
This image file contains three executables, each of which is
used to launch the next-stage payload, ultimately paving the way
for a backdoor that lets the threat actor remotely access the
infected system.
Furthermore, the fee structure spreadsheet is password-protected
in a bid to convince the target into enabling macros, thereby
initiating the malicious actions. A metadata analysis of the file
shows that it was created on October 14, 2022 by a user named
Wolf.
DEV-0139 has also been linked to an alternative attack sequence
in which an MSI package for a fake application named
“CryptoDashboardV2” is delivered in place of a malicious Excel
document to deploy the same implant.
The backdoor mainly enables remote access to the host by
gathering information from the targeted system and connecting to a
command-and-control (C2) server to receive additional commands.
“The cryptocurrency market remains a field of interest for
threat actors,” Microsoft said. “Targeted users are identified
through trusted channels to increase the chance of success.”
In recent years, Telegram has not only witnessed widespread adoption[8]
in the cryptocurrency industry, but also been co-opted by threat
actors looking to discuss zero-day vulnerabilities, offer stolen
data, and market their services through the popular messaging
platform.
“With users losing confidence in the anonymity offered by
forums, illicit marketplaces are increasingly turning to Telegram,”
Positive Technologies disclosed[9]
in a new study of 323 public Telegram channels and groups with over
one million subscribers in total.
“The number of unique cyberattacks is constantly growing, and
the market for cybercriminal services is expanding and moving into
ordinary social media and messaging apps, thereby significantly
lowering the entry threshold for cybercriminals.”
Found this article interesting? Follow us on Twitter [10] and LinkedIn[11] to read more exclusive
content we post.
References
- ^
Lazarus
Group (thehackernews.com) - ^
said
(www.microsoft.com) - ^
VIP
program (www.binance.com) - ^
designed
(learn.bybit.com) - ^
reward
(help.crypto.com) - ^
high-volume traders
(www.kraken.com) - ^
Microsoft Excel document
(www.virustotal.com) - ^
widespread adoption
(techcrunch.com) - ^
disclosed
(www.ptsecurity.com) - ^
Twitter
(twitter.com) - ^
LinkedIn
(www.linkedin.com)
Read more https://thehackernews.com/2022/12/microsoft-alerts-cryptocurrency.html