hacking campaign aimed at government agencies in India and
residents of Hong Kong intending to steal sensitive information,
cybersecurity firm Malwarebytes revealed in the latest
report shared with The Hacker News.
The attacks were observed during the first week of July,
coinciding the passage of controversial
security law[2] in Hong Kong and India’s
ban of 59 China-made apps over privacy concerns, weeks after a
violent
skirmish[3] along the Indo-China
border.
Attributing the attack with “moderate confidence” to a new
Chinese APT group, Malwarebytes said they were able to track their
activities based on the “unique phishing attempts” designed to
compromise targets in India and Hong Kong.
The operators of the APT group have leveraged at least three
different Tactics, Techniques, and Procedures (TTPs), using
spear-phishing emails to drop variants of Cobalt Strike and MgBot
malware, and bogus Android applications to gather call records,
contacts, and SMS messages.
“The lures used in this campaign indicate that the threat actor
may be targeting the Indian government and individuals in Hong
Kong, or at least those who are against the new security law issued
by China,” the firm said.
Using Spear-Phishing to Install MgBot Malware
The first variant, observed on July 2, alerted recipients with the
“gov.in” domain stating some of their email addresses had been
leaked and that they are to complete a security check before July
5.
The emails come attached with a “Mail security check.docx”
purportedly from the Indian Government Information Security Center.
Upon opening, it employs template injection[4]
to download a remote template and execute a heavily obfuscated
variant of Cobalt
Strike[5].
out the malicious Cobalt Strike payload for an updated version of
MgBot malware.
And in the third version seen in the wild on July 5, the
researchers observed the APT using an entirely different embedded
document with a statement about Hong Kong from the UK Prime
Minister Boris Johnson allegedly promising to admit three million
Hong Kongers to the country.
The malicious commands to download and drop the loader — which
are encoded within the documents — are executed using the dynamic
data exchange (DDE[6]) protocol, an
interprocess communication system that allows data to be
communicated or shared between Windows applications.
A RAT With Several Capabilities
The dropped loader (“ff.exe”) masquerades as a Realtek Audio
Manager tool and contains four embedded resources, two of which are
written in Simplified Chinese.
This, along with the use of DDE and template injection, suggests
the campaign could be the handiwork of a China-based threat actor,
given the prior history
of attacks that
took advantage of the same TTPs.
[7][8]
Subsequently, the loader escalates its privileges through a CMSTP bypass
before installing the final payload, while also taking steps to
avoid detection by debuggers and security software.
To thwart static analysis, “the code is self modifying which
means it alters its code sections during runtime,” the researchers
said.
“It uses ‘GetTickCount’ and ‘QueryPerformanceCounter’ API calls
to detect the debugger environment. To detect if it is running in a
virtual environment, it uses anti-vm detection instructions such as
‘sldt’ and ‘cpid’ that can provide information about the processor
and also checks Vmware IO ports (VMXH).”
Ultimately, it’s this final malware executable (“pMsrvd.dll”)
that’s used to conduct the malicious activities, which it does by
posing as a “Video Team Desktop App.”
of establishing a connection to a remote command-and-control (C2)
server located in Hong Kong, it has the ability to capture
keystrokes, screenshots, and manage files and processes.
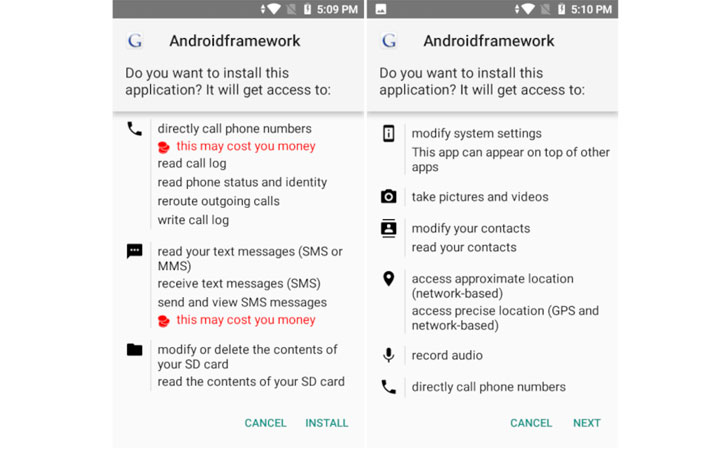
What’s more, the researchers also found several malicious
Android applications as part of the group’s toolset that comes
equipped with RAT features, such as audio and screen recording and
functions to triangulate a phone’s location and exfiltrate
contacts, call logs, SMS, and web history.
Interestingly, it appears this new China APT group has been
active at least since 2014, with its TTPs linked to at least three
different attacks in 2014[10], 2018[11], and March
2020[12]. In all their
campaigns, the actor used a variant of MgBot to meet its
objectives.
References
- ^
Malwarebytes
(blog.malwarebytes.com) - ^
controversial security law
(en.wikipedia.org) - ^
violent skirmish
(www.bbc.com) - ^
template injection
(attack.mitre.org) - ^
Cobalt Strike
(malpedia.caad.fkie.fraunhofer.de) - ^
DDE
(en.wikipedia.org) - ^
prior history
(www.pwc.co.uk) - ^
attacks
(www.elastic.co) - ^
CMSTP bypass
(attack.mitre.org) - ^
2014
(www.virusbulletin.com) - ^
2018
(www.virustotal.com) - ^
March 2020
(www.virustotal.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/3zFHOz2dCVg/chinese-hackers-hong-kong-india.html