Cybersecurity researchers have exposed the operations of an
Android malware vendor who teamed up with a second threat actor to
market and sell a remote access Trojan (RAT) capable of device
takeover and exfiltration of photos, locations, contacts, and
messages from popular apps such as Facebook, Instagram, WhatsApp,
Skype, Telegram, Kik, Line, and Google Messages.
The vendor, who goes by the name of “Triangulum” in a
number of darknet forums, is alleged to be a 25-year-old man of
Indian origin, with the individual opening up shop to sell the
malware three years ago on June 10, 2017, according to an analysis
published by Check Point[1]
Research today.
“The product was a mobile RAT, targeting Android devices and
capable of exfiltration of sensitive data from a C&C server,
destroying local data – even deleting the entire OS, at times,” the
researchers said.
An Active Underground Market for Mobile Malware
Piecing together Triangulum’s trail of activities, the
cybersecurity firm said the malware developer — aside from drumming
up publicity for the RAT — also looked for potential investors and
partners in September 2017 to show off the tool’s features before
offering the tool for sale.
Triangulum, subsequently, is believed to have gone off the grid
for about a year-and-a-half, with no signs of activity on the
darknet, only to resurface on April 6, 2019, with another product
called “Rogue,” this time in collaboration with another adversary
named “HeXaGoN Dev,” who specialized in the development of
Android-based RATs.
Noting that Triangulum had previously purchased several malware
products offered by HeXaGoN Dev, Check Point said Triangulum
advertised his products on different darknet forums with
well-designed infographics listing the full features of the RAT.
Furthermore, HeXaGoN Dev posed as a potential buyer in a bid to
attract more customers.
While the 2017 product was sold for a flat $60 as a lifetime
subscription, the vendors pivoted to a more financially-viable
model in 2020 by charging customers anywhere between $30 (1 month)
to $190 (permanent access) for the Rogue malware.
Interestingly, Triangulum’s attempts to expand to the Russian
darknet market were met with failure following the actor’s refusal
to share demo videos on the forum post advertising the product.
From Cosmos to Dark Shades to Rogue
Rogue (v6.2) — which appears to be the latest iteration of a
malware called Dark Shades (v6.0) that initially sold by HeXaGoN
Dev before being purchased by Triangulum in August 2019 — also
comes with features taken from a second malware family called
Hawkshaw, whose source code became public in 2017.
“Triangulum didn’t develop this creation from scratch, he took
what was available from both worlds, open-source and the darknet,
and united these components,” the researchers said.
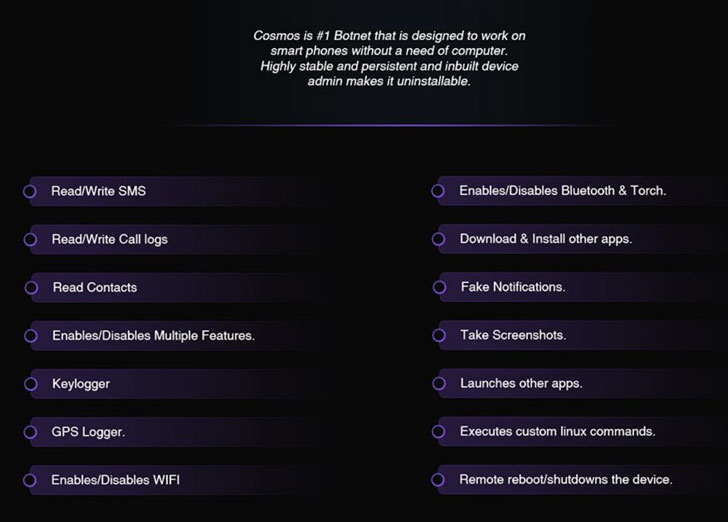
Dark Shades, as it turns out, is a “superior successor” to
Cosmos, a separate RAT sold by the HeXaGoN Dev actor, thus making
the sale of Cosmos redundant.
Rogue is marketed as a RAT “made to execute commands with
incredible features without a need of computer (sic),” with
additional capabilities to control the infected clients remotely
using a control panel or a smartphone.
Indeed, the RAT boasts of a wide range of features to gain
control over the host device and exfiltrate any kind of data (such
as photos, location, contacts, and messages), modify the files on
the device, and even download additional malicious payloads, while
ensuring that the user grants intrusive permissions to carry out
its nefarious activities.
It’s also engineered to thwart detection by hiding the icon from
the user’s device, circumvent Android security restrictions by
exploiting accessibility features to log user actions, and
registers its own notification service to snoop on every
notification that pops up on the infected phone.
What’s more, stealth is built into the tool. Rogue uses Google’s
Firebase infrastructure as a command-and-control (C2) server to
disguise its malicious intentions, abusing the platform’s cloud messaging[2]
feature to receive commands from the server, and Realtime
Database[3] and Cloud Firestore[4]
to upload amassed data and documents from the victim device.
Rogue Suffered a Leak in April 2020
Triangulum may be currently active and expanding his clientele,
but in April 2020, the malware ended up getting leaked.
ESET researcher Lukas Stefanko, in a tweet[5]
on April 20 last year, said the backend source code of the Rogue
Android botnet was published in an underground forum, noting “it
has lot of security issues,” and that “it is new naming for Dark
Shades V6.0 (same developer).”
But despite the leakage, Check Point researchers note that the
Triangulum team still receives messages on the actor’s home Darknet
forum from interested customers.
“Mobile malware vendors are becoming far more resourceful on the
dark net. Our research gives us a glimpse into the craziness of the
dark net: how malware evolves, and how difficult it is to now
track, classify and protect against them in an effective way,”
Check Point’s Head of Cyber Research, Yaniv Balmas, said.
“The underground market is still like the wild-west in a sense,
which makes it very hard to understand what is a real threat and
what isn’t.”
References
- ^
Check
Point (blog.checkpoint.com) - ^
cloud
messaging (firebase.google.com) - ^
Realtime
Database (firebase.google.com) - ^
Cloud
Firestore (firebase.google.com) - ^
tweet
(malpedia.caad.fkie.fraunhofer.de)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/_mOsbV5_NvM/experts-sound-alarm-on-new-android.html