Ivanti, the company behind Pulse Secure VPN appliances, has
published a security advisory for a high severity vulnerability
that may allow an authenticated remote attacker to execute
arbitrary code with elevated privileges.
“Buffer Overflow in Windows File Resource Profiles in 9.X allows
a remote authenticated user with privileges to browse SMB shares to
execute arbitrary code as the root user,” the company said[1]
in an alert published on May 14. “As of version 9.1R3, this
permission is not enabled by default.”
The flaw, identified as CVE-2021-22908, has a CVSS score of 8.5
out of a maximum of 10 and impacts Pulse Connect Secure versions
9.0Rx and 9.1Rx. In a report detailing the vulnerability, the CERT
Coordination Center said the issue stems from the gateway’s ability
to connect to Windows file shares through a number of CGI endpoints
that could be leveraged to carry out the attack.
“When specifying a long server name for some SMB operations, the
‘smbclt’ application may crash due to either a stack buffer
overflow or a heap buffer overflow, depending on how long of a
server name is specified,” CERT/CC detailed[2] in a vulnerability note
published on Monday, adding it was able to trigger the vulnerable
code by targeting the CGI script ‘/dana/fb/smb/wnf.cgi.’
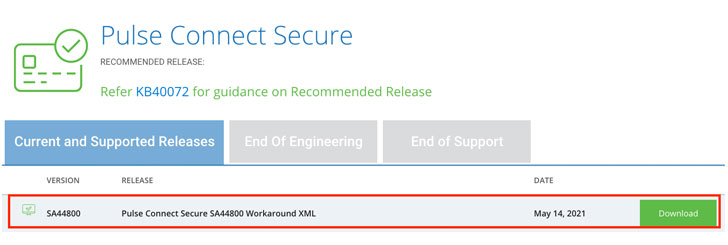
Pulse Secure customers are recommended to upgrade to PCS Server
version 9.1R.11.5 when it becomes available. In the interim, Ivanti
has published a workaround file (‘Workaround-2105.xml’) that can be
imported to disable the Windows File Share Browser feature by
adding the vulnerable URL endpoints to a blocklist and thus
activate necessary mitigations to protect against this
vulnerability.
It bears noting that users running PCS versions 9.1R11.3 or
below would need to import a different file named ‘Workaround-2104.xml,[3]‘ necessitating that the
PCS system is running 9.1R11.4 before applying the safeguards in
‘Workaround-2105.xml.’
While Ivanti has recommended turning off Windows File Browser on
the Admin UI by disabling the option ‘Files, Window [sic]’ for
specific user roles, CERT/CC found the steps were inadequate to
protect against the flaw during its testing.
“The vulnerable CGI endpoints are still reachable in ways that
will trigger the ‘smbclt’ application to crash, regardless of
whether the ‘Files, Windows’ user role is enabled or not,” it
noted.
“An attacker would need a valid DSID and ‘xsauth’ value from an
authenticated user to successfully reach the vulnerable code on a
PCS server that has an open Windows File Access policy.”
The disclosure of a new flaw arrives weeks after the Utah-based
IT software company patched[4]
multiple critical security vulnerabilities in Pulse Connect Secure
products, including CVE-2021-22893, CVE-2021-22894, CVE-2021-22899,
and CVE-2021-22900, the first of which was found to be actively
exploited in the wild[5]
by at least two different threat actors.
References
- ^
said
(kb.pulsesecure.net) - ^
detailed
(kb.cert.org) - ^
Workaround-2104.xml,
(kb.pulsesecure.net) - ^
patched
(thehackernews.com) - ^
exploited in the wild
(thehackernews.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/49QIpwJmZ30/new-high-severity-vulnerability.html