A new research published by a group of academics has found that
anti-virus programs for Android continue to remain vulnerable
against different permutations of malware, in what could pose a
serious risk as malicious actors evolve their toolsets to better
evade analysis.
“Malware writers use stealthy mutations (morphing/obfuscations)
to continuously develop malware clones, thwarting detection by
signature based detectors,” the researchers said[1]. “This attack of clones
seriously threatens all the mobile platforms, especially
Android.”
The findings were published in a study last week by researchers
from Adana Science and Technology University, Turkey, and the
National University of Science and Technology, Islamabad,
Pakistan.
Unlike iOS, apps can be downloaded from third-party sources on
Android devices, raising the possibility that unwitting users can
install unverified and lookalike apps that clone a legitimate app’s
functionality but are built to trick targets into downloading apps
laced with fraudulent code that are capable of stealing sensitive
information.
What’s more, malware authors can expand on this technique to
develop multiple clones of the rogue software with varying levels
of abstraction and obfuscation to disguise their true intent and
slip through the defense barriers created by anti-malware
engines.
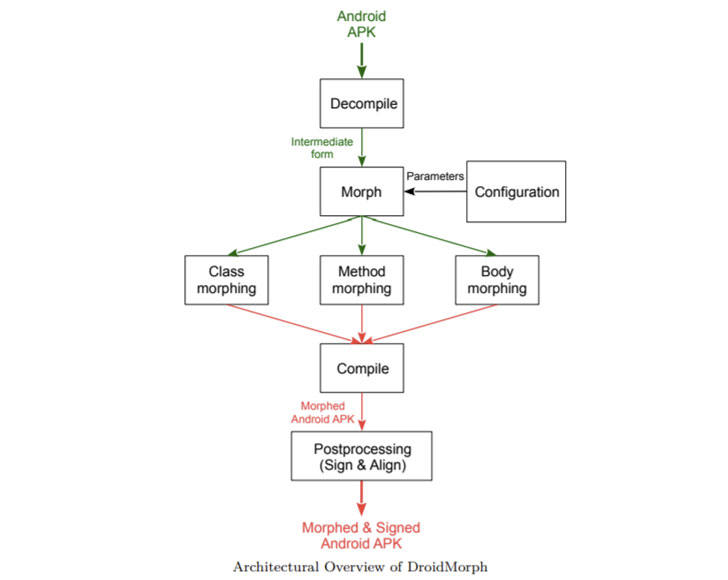
To test and evaluate the resilience of commercially available
anti-malware products against this attack, the researchers
developed a tool called DroidMorph, which allows Android
applications (APKs) to be “morphed” by decompiling the files to an
intermediate form that’s then modified and compiled to create
clones, both benign and malware.
Morphing could be at different levels, the researchers noted,
such as those that involve changing the class and method names in
the source code or something non-trivial that could alter the
execution flow of the program, including the call
graph[2] and the control-flow graph[3].
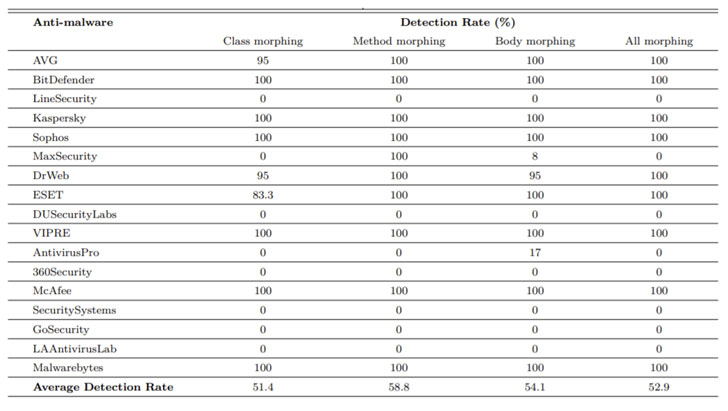
In a test conducted using 1,771 morphed APK variants generated
through DroidMorph, the researchers found that 8 out of 17 leading
commercial anti-malware programs failed to detect any of the cloned
applications, with an average detection rate of 51.4% for class
morphing, 58.8% for method morphing, and 54.1% for body morphing
observed across all programs.
The anti-malware programs that were successfully bypassed
include LineSecurity, MaxSecurity, DUSecurityLabs, AntivirusPro,
360Security, SecuritySystems, GoSecurity, and LAAntivirusLab.
As future work, the researchers outlined that they intend to add
more obfuscations at different levels as well as enable morphing of
metadata information such as permissions that are embedded in an
APK file with an aim to bring down the detection rates.
References
- ^
said
(arxiv.org) - ^
call
graph (en.wikipedia.org) - ^
control-flow graph
(en.wikipedia.org)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/PKnbtFCCNiA/droidmorph-shows-popular-android.html