A critical vulnerability in SonicWall VPN appliances that was
believed to have been patched last year has been now found to be
“botched,” with the company leaving a memory leak flaw unaddressed,
until now, that could permit a remote attacker to gain access to
sensitive information.
The shortcoming was rectified in an update rolled out to SonicOS
on June 22.
Tracked as CVE-2021-20019[1]
(CVSS score: 5.3), the vulnerability is the consequence of a memory
leak when sending a specially-crafted unauthenticated HTTP request,
culminating in information disclosure.
It’s worth noting that SonicWall’s decision to hold back the
patch comes amid multiple[2]
zero-day[3]
disclosures[4]
affecting its remote access VPN and email security products that
have been exploited in a series of in-the-wild attacks to deploy
backdoors and a new strain of ransomware called FIVEHANDS.
Howevere, there is no evidence that the flaw is being exploited
in the wild.
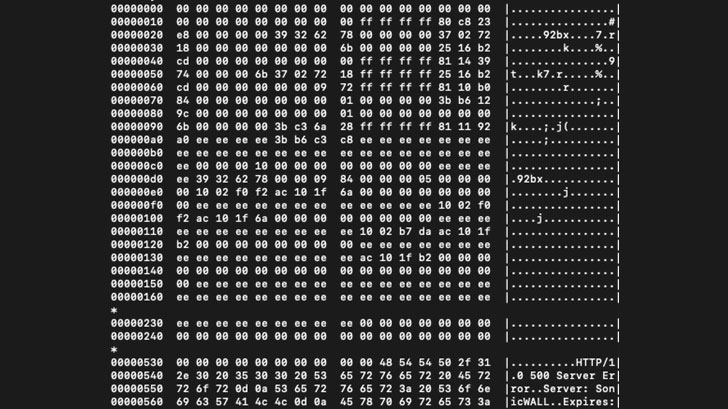 |
| Memory Dump PoC |
“SonicWall physical and virtual firewalls running certain
versions of SonicOS may contain a vulnerability where the HTTP
server response leaks partial memory,” SonicWall said in an
advisory[5]
published Tuesday. “This can potentially lead to an internal
sensitive data disclosure vulnerability.”
The original flaw, identified as CVE-2020-5135[6]
(CVSS score: 9.4), concerned a buffer overflow vulnerability in
SonicOS that could allow a remote attacker to cause
denial-of-service (DoS) and potentially execute arbitrary code by
sending a malicious request to the firewall.
While SonicWall rolled out a patch in October 2020, additional
testing undertaken by cybersecurity firm Tripwire revealed a memory
leak as a “result of an improper fix for CVE-2020-5135,” according
to security researcher Chris Young, who reported the new issue to
SonicWall on October 6, 2020.
“As a one- or two-line fix with minimal impact, I had expected
that a patch would probably come out quickly but, fast-forward to
March and I still had not heard back,” Young noted[7]
in a write-up on Tuesday. “I reconnected with their PSIRT on March
1, 2021 for an update, but ultimately it took until well into June
before an advisory could be released.”
References
- ^
CVE-2021-20019
(psirt.global.sonicwall.com) - ^
multiple
(thehackernews.com) - ^
zero-day
(thehackernews.com) - ^
disclosures
(thehackernews.com) - ^
advisory
(www.sonicwall.com) - ^
CVE-2020-5135
(psirt.global.sonicwall.com) - ^
noted
(www.tripwire.com)
Read more http://feedproxy.google.com/~r/TheHackersNews/~3/F-0UTEffuRc/sonicwall-left-vpn-flaw-partially.html
