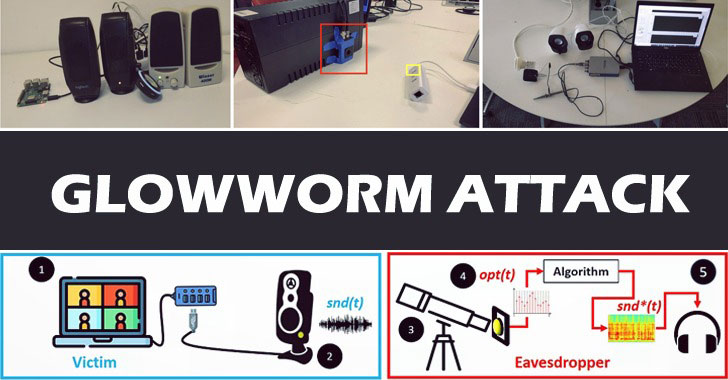
A novel technique leverages optical emanations from a device’s
power indicator LED to recover sounds from connected peripherals
and spy on electronic conversations from a distance of as much as
35 meters.
Dubbed the “Glowworm attack[1],” the findings were
published by a group of academics from the Ben-Gurion University of
the Negev earlier this week, describing the method as “an optical
TEMPEST[2]
attack that can be used by eavesdroppers to recover sound by
analysing optical measurements obtained via an electro-optical
sensor directed at the power indicator LED of various devices.”
Accompanying the experimental setup is an optical-audio
transformation (OAT) that allows for retrieving sound by isolating
the speech from the optical measurements obtained by directing an
electro-optical sensor at the device’s power indicator LED.
TEMPEST is the codename for unintentional intelligence-bearing
emanations produced by electronic and electromechanical
information-processing equipment.
Glowworm builds on a similar attack called Lamphone that was
demonstrated by the same researchers last year and enables the
recovery of sound from a victim’s room that contains an overhead
hanging bulb.
While both methods retrieve sound from light via an
electro-optical sensor, they are also different in that while the
Lamphone[3]
attack “is a side-channel attack that exploits a light bulb’s
miniscule vibrations, which are the result of sound waves hitting
the bulb,” Glowworm is a “TEMPEST attack that exploits the way that
electrical circuits were designed. It can recover sound from
devices like USB hub splitters that do not move in response to the
acoustic information played by the speakers.”
The attack hinges on the optical correlation between the sound
that is played by connected speakers and the intensity of their
power indicator LED, which are not only connected directly to the
power line but also that the intensity of a device’s power
indicator LED is influenced by the power consumption. What’s more,
the quality of the sound recovered is proportional to the quality
of the equipment used by the eavesdropper.
In a real-world scenario, the threat model takes aim at the
speech generated by participants in a virtual meeting platform such
as Zoom, Google Meet, and Microsoft Teams, with the malicious party
located in a room in an adjacent building, enabling the adversary
to recover sound from the power indicator LED of the speakers.
In an indirect attack scenario where the power indicator LED
isn’t visible from outside the room, the eavesdropper can recover
sound from the power indicator LED of the device used to provide
the power to the speaker.
Although such attacks can be countered on the consumer side by
placing a black tape over a device’s power indicator LED, the
researchers recommend device manufacturers to integrate a capacitor
or an operational amplifier to eliminate the power consumption
fluctuations that occur when the speakers produce sound.
“While the cost of our countermeasures might seem negligible,
given the likelihood that the devices are mass produced, the
addition of a component to prevent the attack could cost a
manufacturer millions of dollars,” the researchers said. “Given the
cost-driven nature of consumers and the profit-driven nature of
manufacturers, known vulnerabilities are often ignored as a means
of reducing costs. This fact may leave many electrical circuits
vulnerable to Glowworm attack for years to come.”