A mix of banking applications, cryptocurrency wallets, and
shopping apps from the U.S. and Spain are the target of a newly
discovered Android trojan that could enable attackers to siphon
personally identifiable information from infected devices,
including banking credentials and open the door for on-device
fraud.
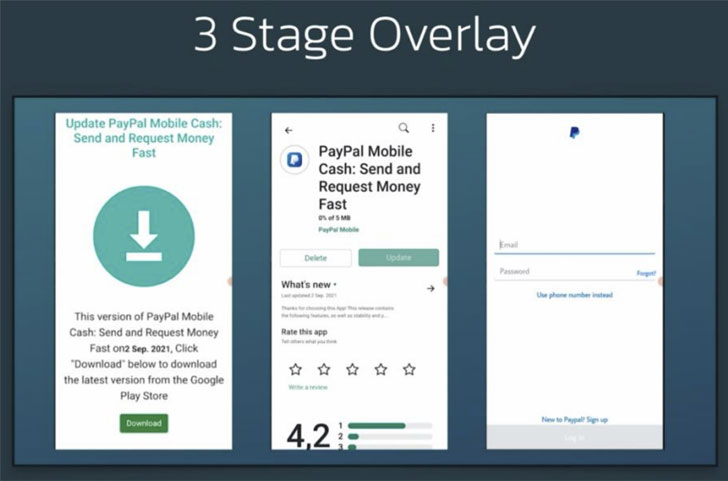
Dubbed S.O.V.A. (referring to the Russian word for owl), the
current version of the banking malware comes with myriad features
to steal credentials and session cookies through web overlay
attacks, log keystrokes, hide notifications, and manipulate the
clipboard to insert modified cryptocurrency wallet addresses, with
future plans to incorporate on-device fraud through VNC[1], carry out DDoS attacks,
deploy ransomware, and even intercept two-factor authentication
codes.
The malware was discovered in the beginning of August 2021 by
researchers from Amsterdam-based cybersecurity firm
ThreatFabric.
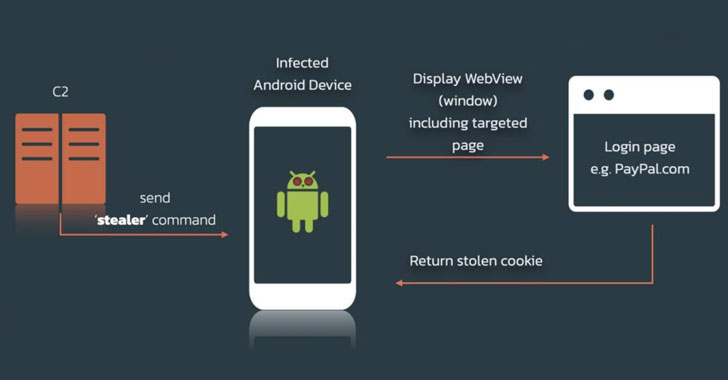
Overlay attacks typically involve the theft of confidential user
information using malware that overlays its own windows on top of
another program. On the other hand, the pilfering of valid session
cookies is particularly nasty as it allows the criminals to log in
and take over accounts from the users without the need for knowing
the banking credentials.
“The second set of features, added in the future developments,
are very advanced and would push S.O.V.A. into a different realm
for Android malware, making it potentially one of the most advanced
bots in circulation, combining banking malware with automation and
botnet capabilities,” ThreatFabric said[2]
in a report shared with The Hacker News.
Although the malware is believed to be in its nascent stages of
development, S.O.V.A.’s developers have been advertising the
product on hacking forums, looking to recruit testers to trial the
malware on a large number of devices and its bot capabilities. “Not
redistribution of Cerberus[3]/Anubis[4], the bot is written from
scratch,” the forum post read.
“[S.O.V.A.] is still a project in its infancy, and now provides
the same basic features as most other modern Android banking
malware,” the researchers said. “However, the author behind this
bot clearly has high expectations for his product, and this is
demonstrated by the author’s dedication to test S.O.V.A. with third
parties, as well as by S.O.V.A.’s explicit feature roadmap.”