Cybersecurity researchers have detailed a new campaign that
likely targets entities in Southeast Asia with a previously
unrecognized Linux malware that’s engineered to enable remote
access to its operators, in addition to amassing credentials and
function as a proxy server.
The malware family, dubbed “FontOnLake” by Slovak
cybersecurity firm ESET, is said to feature “well-designed modules”
that are continuously being upgraded with new features, indicating
an active development phase. Samples uploaded to VirusTotal point
to the possibility that the very first intrusions utilizing this
threat have been happening as early as May 2020.
Avast[1]
and Lacework Labs[2]
are tracking the same malware under the moniker HCRootkit.
“The sneaky nature of FontOnLake’s tools in combination with
advanced design and low prevalence suggest that they are used in
targeted attacks,” ESET researcher Vladislav Hrčka said[3]. “To collect data or
conduct other malicious activity, this malware family uses modified
legitimate binaries that are adjusted to load further components.
In fact, to conceal its existence, FontOnLake’s presence is always
accompanied by a rootkit. These binaries are commonly used on Linux
systems and can additionally serve as a persistence mechanism.”
FontOnLake’s toolset includes three components that consist of
trojanized versions of legitimate Linux utilities that are used to
load kernel-mode rootkits and user-mode backdoors, all of which
communicate with one another using virtual files. The C++-based
implants themselves are designed to monitor systems, secretly
execute commands on networks, and exfiltrate account
credentials.
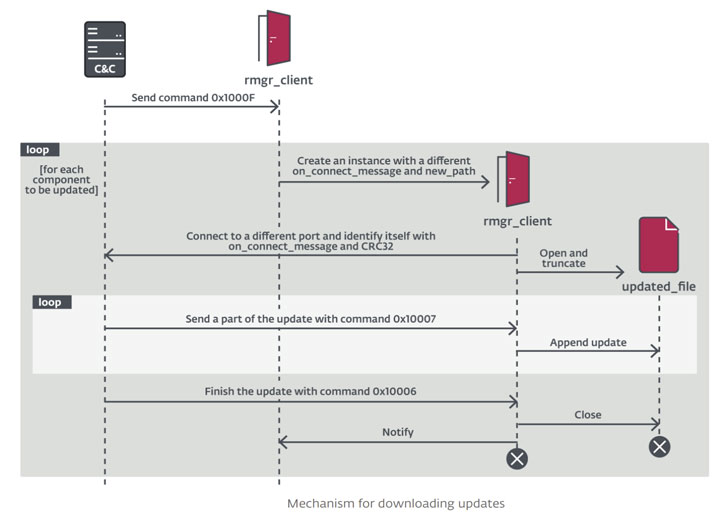
A second permutation of the backdoor also comes with
capabilities to act as a proxy, manipulate files, download
arbitrary files, while a third variant, besides incorporating
features from the other two backdoors, is equipped to execute
Python scripts and shell commands.
ESET said it found two different versions of the Linux rootkit
that’s based on an open-source project called Suterusu[4] and share overlaps in
functionality, including hiding processes, files, network
connections, and itself, while also being able to carry out file
operations, and extract and execute the user-mode backdoor.
It’s currently not known how the attackers gain initial access
to the network, but the cybersecurity company noted that the threat
actor behind the attacks is “overly cautious” to avoid leaving any
tracks by relying on different, unique command-and-control (C2)
servers with varying non-standard ports. All the C2 servers
observed in the VirusTotal artifacts are no longer active.
“Their scale and advanced design suggest that the authors are
well versed in cybersecurity and that these tools might be reused
in future campaigns,” Hrčka said. “As most of the features are
designed just to hide its presence, relay communication, and
provide backdoor access, we believe that these tools are used
mostly to maintain an infrastructure which serves some other,
unknown, malicious purposes.”