Mozilla is beginning to roll out Firefox 95 with a new
sandboxing technology called RLBox that prevents untrusted code and
other security vulnerabilities from causing “accidental defects as
well as supply-chain attacks.”
Dubbed “RLBox[1]” and implemented in
collaboration with researchers at the University of California San
Diego and the University of Texas, the improved protection
mechanism is designed to harden the web browser against potential
weaknesses in off-the-shelf libraries used to render audio, video,
fonts, images, and other content.
To that end, Mozilla is incorporating “fine-grained sandboxing”
into five modules, including its Graphite[2]
font rendering engine, Hunspell[3]
spell checker, Ogg[4]
multimedia container format, Expat[5]
XML parser, and Woff2[6]
web font compression format.
The framework uses WebAssembly[7], an open standard that
defines a portable binary-code format for executable programs that
can be run on modern web browsers, to isolate potentially unsafe
code, a prototype[8]
version of which was shipped in February 2020 to Mac and Linux
users.
All major browsers are designed to run web content in their own
sandboxed environment as a means to counter malicious sites from
exploiting a browser vulnerability to compromise the underlying
operating system. Firefox also implements Site Isolation[9], which loads each
website separately in its own process and, as a result, blocks
arbitrary code hosted on a rogue website from accessing
confidential information stored in other sites.
The problem with these approaches, according to Mozilla, is that
attacks often work by stringing together two or more flaws that aim
to breach the sandboxed process containing the suspicious site and
break out of the isolation barriers, effectively undermining the
security measures put in place.
“Retrofitting isolation can be labor-intensive, very prone to
security bugs, and requires critical attention to performance,” the
researchers noted in a paper[10] that formed the basis
for the feature. RLBox “minimizes the burden of converting Firefox
to securely and efficiently use untrusted code.”
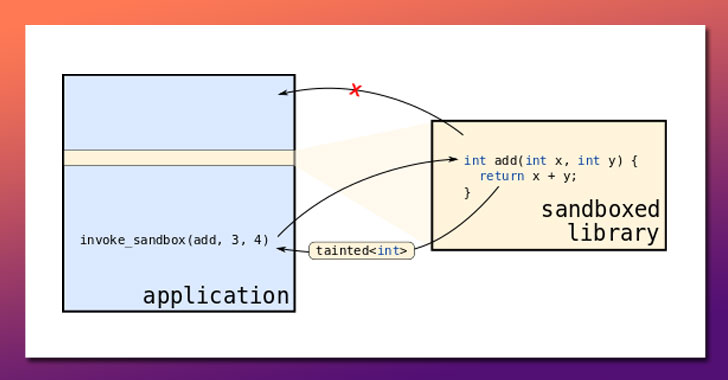
RLBox aims to increase browser security by sandboxing
third-party C/C++-language libraries that are vulnerable to attacks
from interfering with the rest of the browser. Put differently, the
goal is to isolate these libraries in lightweight sandboxes such
that threat actors can’t exploit vulnerabilities in these
subcomponents to impact the rest of the browser.
“Rather than hoisting the code into a separate process, we
instead compile it into WebAssembly and then compile that
WebAssembly into native code,” Mozilla’s principal engineer Bobby
Holley said[11]. “The transformation
places two key restrictions on the target code: it can’t jump to
unexpected parts of the rest of the program, and it can’t access
memory outside of a specified region,” adding “even a zero-day
vulnerability in any of [these libraries] should pose no threat to
Firefox.”
Mozilla noted that cross-platform sandboxing for Graphite,
Hunspell, and Ogg is shipping in Firefox 95 across desktop and
mobile versions of the browser, while Expat and Woff2 are expected
to gain support for the feature in Firefox 96.
References
- ^
RLBox
(plsyssec.github.io) - ^
Graphite
(scripts.sil.org) - ^
Hunspell
(hunspell.github.io) - ^
Ogg (xiph.org) - ^
Expat
(libexpat.github.io) - ^
Woff2
(github.com) - ^
WebAssembly
(developer.mozilla.org) - ^
prototype
(hacks.mozilla.org) - ^
Site
Isolation (thehackernews.com) - ^
paper
(arxiv.org) - ^
said
(hacks.mozilla.org)
Read more https://thehackernews.com/2021/12/latest-firefox-95-includes-rlbox.html