VMWare has shipped updates to Workstation, Fusion, and ESXi
products to address an “important” security vulnerability that
could be weaponized by a threat actor to take control of affected
systems.
The issue relates to a heap-overflow vulnerability — tracked as
CVE-2021-22045 (CVSS score: 7.7) — that, if
successfully exploited, results in the execution of arbitrary code.
The company credited Jaanus Kääp, a security researcher with
Clarified Security, for reporting the flaw.
“A malicious actor with access to a virtual machine with CD-ROM
device emulation may be able to exploit this vulnerability in
conjunction with other issues to execute code on the hypervisor
from a virtual machine,” VMware said[1]
in an advisory published on January 4.
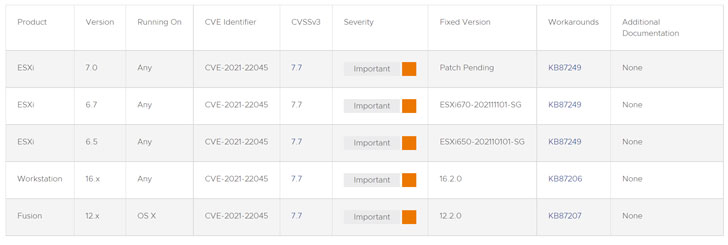
The error affects ESXi versions 6.5, 6.7, and 7.0; Workstation
versions 16.x; and Fusion versions 12.x, with the company yet to
release a patch for ESXi 7.0. In the interim, the company is
recommending[2]
users to disable all CD-ROM/DVD devices on all running virtual
machines to prevent any potential exploitation —
- Log in to a vCenter Server system using the vSphere Web
Client. - Right-click the virtual machine and click Edit Settings.
- Select the CD/DVD drive and uncheck “Connected” and “Connect at
power on” and remove any attached ISOs.
With VMware’s virtualization solutions widely deployed across
enterprises, it’s no surprise that its products[3]
have emerged[4]
as a popular[5]
choice[6]
for threat actors[7]
to stage a multitude of attacks against vulnerable networks. To
mitigate the risk of infiltration, it’s recommended that
organizations move quickly to apply the necessary updates.
References
Read more https://thehackernews.com/2022/01/vmware-patches-important-bug-affecting.html