Cybersecurity researchers on Tuesday took the wraps off a
multi-stage espionage campaign targeting high-ranking government
officials overseeing national security policy and individuals in
the defense industry in Western Asia.
The attack is unique as it leverages Microsoft OneDrive as a
command-and-control (C2) server and is split into as many as six
stages to stay as hidden as possible, Trellix, a new company
created following the merger of security firms McAfee Enterprise
and FireEye, said in a report shared with The Hacker News.
First signs of activity associated with the covert operation are
said to have commenced as early as June 18, 2021, with two victims
reported on September 21 and 29, followed by 17 more in a short
span of three days between October 6 and 8.
Trellix attributed the attacks with moderate confidence to the
Russia-based APT28 group, the threat actor behind the compromise of SolarWinds[1] in 2020, based on
similarities in the source code as well as in the attack indicators
and geopolitical objectives.
“We are supremely confident that we are dealing with a very
skilled actor based on how infrastructure, malware coding and
operation were set up,” Trellix security researcher Marc Elias
said.
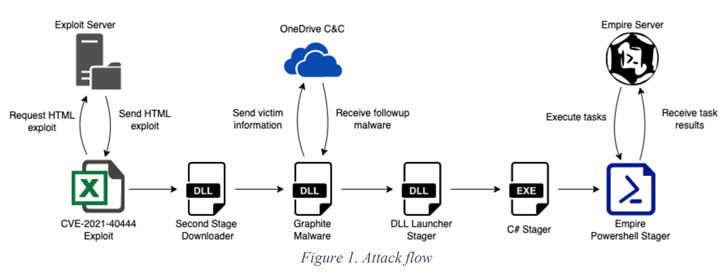
The infection chain begins with the execution of a Microsoft
Excel file containing an exploit for the MSHTML remote code
execution vulnerability (CVE-2021-40444[2]), which is used to run a
malicious binary that acts as the downloader for a third-stage
malware dubbed Graphite.
The DLL executable uses OneDrive as the C2 server via the
Microsoft Graph API to retrieve additional stager malware that
ultimately downloads and executes Empire[3], an open-source
PowerShell-based post-exploitation framework widely abused by
threat actors for follow-on activities.
If anything, the development marks the continued exploitation of
the MSTHML rendering engine flaw, with Microsoft[4]
and SafeBreach Labs[5]
disclosing multiple campaigns that have weaponized the
vulnerability to plant malware and distribute custom Cobalt Strike
Beacon loaders.
References
- ^
compromise of SolarWinds
(thehackernews.com) - ^
CVE-2021-40444
(thehackernews.com) - ^
Empire
(attack.mitre.org) - ^
Microsoft
(thehackernews.com) - ^
SafeBreach Labs
(thehackernews.com)
Read more https://thehackernews.com/2022/01/hackers-exploited-mshtml-flaw-to-spy-on.html