The notorious TrickBot malware is targeting customers of 60
financial and technology companies, including cryptocurrency firms,
primarily located in the U.S., even as its operators have updated
the botnet with new anti-analysis features.
“TrickBot is a sophisticated and versatile malware with more
than 20 modules that can be downloaded and executed on demand,”
Check Point researchers Aliaksandr Trafimchuk and Raman Ladutska
said[1]
in a report published today.
In addition to being both prevalent and persistent, TrickBot has
continually[2]
evolved[3]
its tactics to go past security and detection layers. To that end,
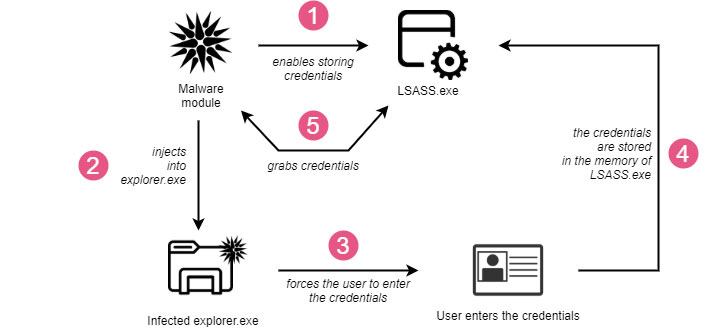
the malware’s “injectDll” web-injects module, which is responsible
for stealing banking and credential data, leverages
anti-deobfuscation techniques to crash the web page and thwart
attempts to scrutinize the source code.
Also put in place are anti-analysis guardrails to prevent
security researchers from sending automated requests to
command-and-control (C2) servers to retrieve fresh web injects.
Another of TrickBot’s key strengths is its ability to propagate
itself, which it achieves by using the “tabDLL” module to steal the
users’ credentials and spread the malware via SMBv1 network share
using the EternalRomance[4]
exploit.
A third crucial module deployed as part of TrickBot infections
is “pwgrabc,” a credential stealer designed to siphon passwords
from web browsers and a number of other applications such as
Outlook, Filezilla, WinSCP, RDP, Putty, OpenSSH, OpenVPN, and
TeamViewer.
“TrickBot attacks high-profile victims to steal the credentials
and provide its operators access to the portals with sensitive data
where they can cause greater damage,” the researchers said, adding
“the operators behind the infrastructure are very experienced with
malware development on a high level as well.”
The findings also come as the TrickBot gang was disclosed as
employing metaprogramming methods[5]
for its Bazar family of malware[6]
to conceal their code and protect against reverse engineering with
the ultimate goal of evading signature-based detection.
References
- ^
said
(research.checkpoint.com) - ^
continually
(thehackernews.com) - ^
evolved
(thehackernews.com) - ^
EternalRomance
(thehackernews.com) - ^
metaprogramming methods
(securityintelligence.com) - ^
Bazar
family of malware (www.cybereason.com)
Read more https://thehackernews.com/2022/02/trickbot-malware-targeted-customers-of.html