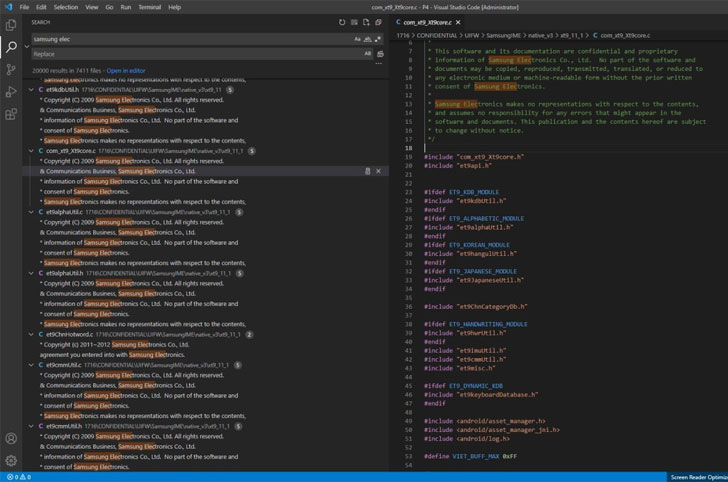
Samsung on Monday confirmed a security breach that resulted in
the exposure of internal company data, including the source code
related to its Galaxy smartphones.
“According to our initial analysis, the breach involves some
source code relating to the operation of Galaxy devices, but does
not include the personal information of our consumers or
employees,” the electronics giant told[1]
Bloomberg.
The South Korean chaebol also confirmed that it doesn’t
anticipate any impact to its business or its customers as a result
of the incident and that it has implemented new security measures
to prevent such breaches in the future.
The confirmation comes after the LAPSUS$ hacking group dumped
190GB of Samsung data on its Telegram channel towards the end of
last week, allegedly exposing the source code for trusted applets
installed within TrustZone[2], algorithms for
biometric authentication, bootloaders for recent devices, and even
confidential data from its chip supplier Qualcomm.
The news of the leak was first reported[3]
by Bleeping Computer on March 4, 2022.
If the name LAPSUS$ rings familiar, it’s the same extortionist
gang that made away a 1TB trove of proprietary data[4] from NVIDIA last month,
namely employee credentials, schematics, driver source code, and
information pertaining to the new graphics chips
The group, which first emerged in late December 2021, also
placed an unusual demand urging the company to open-source its GPU
drivers forever and remove its Ethereum cryptocurrency mining cap
from all NVIDIA 30-series GPUs to prevent more leaks.
It’s not immediately clear if LAPSUS$ has made any similar
demands to Samsung before publishing the information.
The fallout from the NVIDIA leaks has also led to the release[5]
of “over 70,000 employee email addresses and NTLM password hashes,
many of which were subsequently cracked and circulated within the
hacking community.”
That’s not all. Two code-signing certificates included[6]
in cache dump from NVIDIA have been used to sign malicious Windows
drivers and other[7]
tools[8]
often used by hacking crews, namely Cobalt Strike beacons,
Mimikatz, and other remote access trojans.
“Threat actors started on 1st March, a day after torrent [was]
posted,” security researcher Kevin Beaumont said[9]
in a tweet last week.
References
Read more https://thehackernews.com/2022/03/samsung-confirms-data-breach-after.html