Network-attached storage (NAS) appliance maker QNAP on Monday
warned of a recently disclosed Linux vulnerability affecting its
devices that could be abused to elevate privileges and gain control
of affected systems.
“A local privilege escalation vulnerability, also known as
‘Dirty Pipe,’ has been reported to affect the Linux kernel on QNAP
NAS running QTS 5.0.x and QuTS hero h5.0.x,” the company said[1]. “If exploited, this
vulnerability allows an unprivileged user to gain administrator
privileges and inject malicious code.”
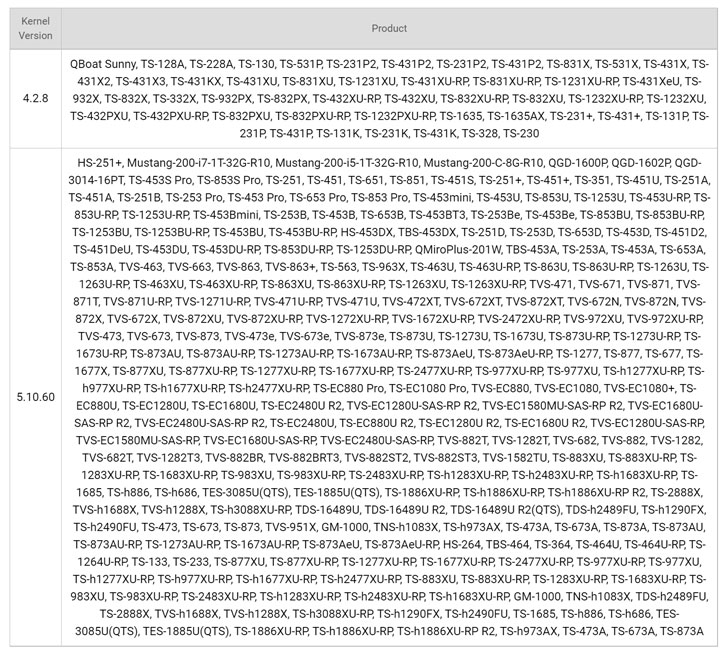
The Taiwanese firm said it’s continuing to thoroughly investigate its product line[2] for the vulnerability
and that there’s no QNAP NAS running QTS 4.x are immune to the
Dirty Pipe flaw.
Tracked as CVE-2022-0847[3]
(CVSS score: 7.8), the shortcoming resides in the Linux kernel that
could permit an attacker to overwrite arbitrary data into any
read-only files and allow for a complete takeover of vulnerable
machines.
The issue has since been fixed in Linux versions 5.16.11,
5.15.25, and 5.10.102 as of February 23, 2022, three days after it
was reported to the Linux kernel security team.
“Currently there is no mitigation available for this
vulnerability,” the company added. “We recommend users to check
back and install security updates as soon as they become
available.”
References
- ^
said
(www.qnap.com) - ^
investigate its product line
(www.qnap.com) - ^
CVE-2022-0847
(thehackernews.com)
Read more https://thehackernews.com/2022/03/dirty-pipe-linux-flaw-affects-wide.html