Two weeks after details emerged about a second data wiper strain
delivered in attacks against Ukraine, yet another destructive
malware has been detected amid Russia’s continuing military
invasion of the country.
Slovak cybersecurity company ESET dubbed the third wiper
“CaddyWiper,” which it said it first observed on
March 14 around 9:38 a.m. UTC. Metadata associated with the
executable (“caddy.exe[1]“) shows that the malware
was compiled at 7:19 a.m. UTC, a little over two hours prior to its
deployment.
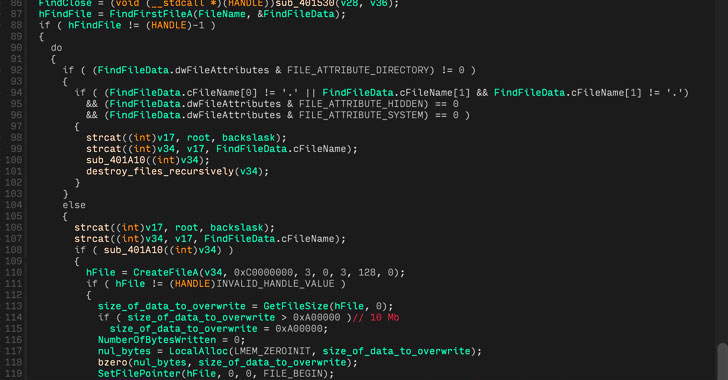
“This new malware erases user data and partition information
from attached drives,” the company said[2]
in a tweet thread. “ESET telemetry shows that it was seen on a few
dozen systems in a limited number of organizations.”
CaddyWiper is notable for the fact that it doesn’t share any
similarities with previously discovered wipers in Ukraine,
including HermeticWiper[3]
(aka FoxBlade or KillDisk) and IsaacWiper[4]
(aka Lasainraw), the two of which have been deployed in systems
belonging to government and commercial entities.
Unlike CaddyWiper, both the HermeticWiper and IsaacWiper malware
families are said to have been in development for months in advance
before their release, with oldest known samples compiled on
December 28 and October 19, 2021, respectively.
But the newly discovered wiper shares one tactical overlap with
HermeticWiper in that the malware, in one instance, was deployed
via the Windows domain controller, indicating that the attackers
had taken control of the Active Directory server.
“Interestingly, CaddyWiper avoids destroying data on domain
controllers,” the company said. “This is probably a way for the
attackers to keep their access inside the organization while still
disturbing operations.”
Microsoft, which has attributed the HermeticWiper attacks to a
threat cluster tracked as DEV-0665, said the “intended objective of
these attacks is the disruption, degradation, and destruction of
targeted resources” in the country.
The development also arrives as cybercriminals have
opportunistically and increasingly capitalized on the conflict to
design phishing lures, including themes of humanitarian assistance
and various types of fundraising, to deliver a variety of backdoors
such as Remcos.
“The global interest in the ongoing war in Ukraine makes it a
convenient and effective news event for cybercriminals to exploit,”
Cisco Talos researchers said[5]. “If a certain topic of
lure is going to increase the chances of a potential victim
installing their payload, they will use it.”
But it’s not just Ukraine that’s been at the receiving end of
wiper attacks. Last week, cybersecurity firm Trend Micro disclosed
details of a .NET-based wiper called RURansom[6]
that has exclusively targeted entities in Russia by encrypting the
files with a randomly generated cryptographic key.
“The keys are unique for each encrypted file and are not stored
anywhere, making the encryption irreversible and marking the
malware as a wiper rather than a ransomware variant,” the
researchers noted.
References
Read more https://thehackernews.com/2022/03/caddywiper-yet-another-data-wiping.html