Cybersecurity researchers have uncovered further links between
BlackCat (aka AlphaV) and BlackMatter ransomware families, the
former of which emerged as a replacement following international
scrutiny last year.
“At least some members of the new BlackCat[1]
group have links to the BlackMatter group, because they modified
and reused a custom exfiltration tool […] and which has only been
observed in BlackMatter activity,” Kaspersky researchers said[2]
in a new analysis.
The tool, dubbed Fendr, has not only been upgraded to include
more file types but also used by the gang extensively to steal data
from corporate networks in December 2021 and January 2022 prior to
encryption, in a popular tactic called double extortion.
The findings come less than a month after Cisco Talos
researchers identified[3]
overlaps in the tactics, techniques, and procedures (TTPs) between
BlackCat and BlackMatter, describing the new ransomware variant as
a case of “vertical business expansion.”
BlackCat stands out for two reasons: it’s an affiliate actor
that has deployed BlackMatter in the past and its malware is
written in Rust, indicating how threat actors are increasingly
pivoting to programming languages[4] with cross-compilation
capabilities.
The group “provides infrastructure, malware samples, ransom
negotiations, and probably cash-out,” the researchers noted.
“Anyone who already has access to compromised environments can use
BlackCat’s samples to infect a target.”
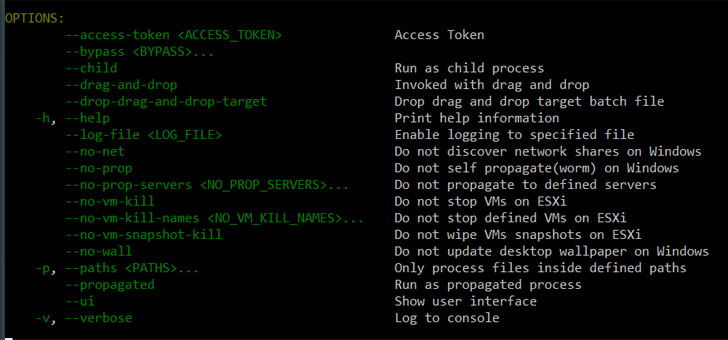
Once executed, the malware gets the Windows system’s MachineGuid[5]
from the registry — a unique key generated during the installation
of the operating system — as well as its UUID, before proceeding to
bypass User Account Control (UAC[6]), delete shadow backups,
and start the encryption process.
“This use of a modified Fendr, also known as ExMatter,
represents a new data point connecting BlackCat with past
BlackMatter activity,” the researchers said.
“The modification of this reused tool demonstrates a more
sophisticated planning and development regimen for adapting
requirements to target environments, characteristic of a maturing
criminal enterprise.”
References
- ^
BlackCat
(thehackernews.com) - ^
said
(securelist.com) - ^
identified
(thehackernews.com) - ^
pivoting
to programming languages
(thehackernews.com) - ^
MachineGuid
(www.nextofwindows.com) - ^
UAC
(attack.mitre.org)
Read more https://thehackernews.com/2022/04/researchers-connect-blackcat-ransomware.html