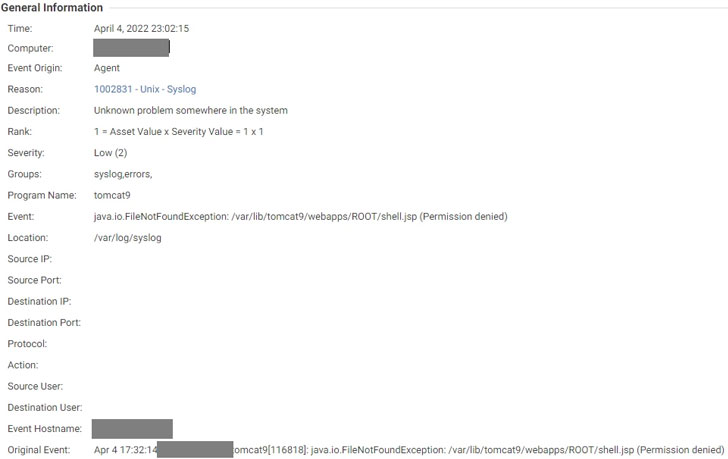
The recently disclosed critical Spring4Shell
vulnerability is being actively exploited by threat actors to
execute the Mirai[1]
botnet
malware[2], particularly in the
Singapore region since the start of April 2022.
“The exploitation allows threat actors to download the Mirai
sample to the ‘/tmp’ folder and execute them after permission
change using ‘chmod[3],'” Trend Micro
researchers Deep Patel, Nitesh Surana, Ashish Verma said[4]
in a report published Friday.
Tracked as CVE-2022-22965[5]
(CVSS score: 9.8), the vulnerability could allow malicious actors
to achieve remote code execution in Spring Core applications under
non-default circumstances, granting the attackers full control over
the compromised devices.
The development comes as the U.S. Cybersecurity and
Infrastructure Security Agency (CISA) earlier this week added[6]
the Spring4Shell vulnerability to its Known Exploited
Vulnerabilities Catalog based on “evidence of active
exploitation.”
This is far from the first time the botnet operators have
quickly moved to add newly publicized flaws to their exploit
toolset. In December 2021, multiple botnets including Mirai and
Kinsing were uncovered[7]
leveraging the Log4Shell vulnerability[8]
to breach susceptible servers on the internet.
Mirai[9], meaning “future” in
Japanese, is the name given to a Linux
malware[10] that has continued to
target networked smart home devices such as IP cameras and routers
and link them together into a network of infected devices known as
a botnet.
The IoT botnet, using the herd of hijacked hardware, can be then
used to commit further attacks, including large-scale phishing
attacks, cryptocurrency mining, click fraud, and distributed
denial-of-service (DDoS) attacks.
To make matters worse, the leak of Mirai’s source code in
October 2016[11] has given birth to
numerous variants[12] such as Okiru, Satori,
Masuta, and Reaper[13], making it an
ever-mutating threat.
Earlier this January, cybersecurity firm CrowdStrike noted that
malware hitting Linux systems increased by 35% in 2021 compared to
2020, with XOR
DDoS[14], Mirai, and Mozi[15] malware families
accounting for more than 22% of Linux-targeted threats observed in
the year.
“The primary purpose of these malware families is to compromise
vulnerable internet-connected devices, amass them into botnets, and
use them to perform distributed denial-of-service (DDoS) attacks,”
the researchers said[16].
References
- ^
Mirai
(malpedia.caad.fkie.fraunhofer.de) - ^
botnet malware
(blog.netlab.360.com) - ^
‘chmod
(en.wikipedia.org) - ^
said
(www.trendmicro.com) - ^
CVE-2022-22965
(thehackernews.com) - ^
added
(thehackernews.com) - ^
uncovered
(www.zscaler.com) - ^
Log4Shell vulnerability
(thehackernews.com) - ^
Mirai
(en.wikipedia.org) - ^
Linux malware
(www.cloudflare.com) - ^
October 2016
(thehackernews.com) - ^
numerous variants
(thehackernews.com) - ^
Reaper
(www.radware.com) - ^
XOR DDoS
(thehackernews.com) - ^
Mozi
(thehackernews.com) - ^
said
(www.crowdstrike.com)
Read more https://thehackernews.com/2022/04/hackers-exploiting-spring4shell.html