Cybersecurity researchers have disclosed a new version of the
SolarMarker malware that packs in new improvements with the goal of
updating its defense evasion abilities and staying under the
radar.
“The recent version demonstrated an evolution from Windows
Portable Executables (EXE files) to working with Windows installer
package files (MSI files),” Palo Alto Networks Unit 42 researchers
said[1]
in a report published this month. “This campaign is still in
development and going back to using executables files (EXE) as it
did in its earlier versions.”
SolarMarker, also called Jupyter, leverages manipulated search
engine optimization (SEO) tactics as its primary infection vector.
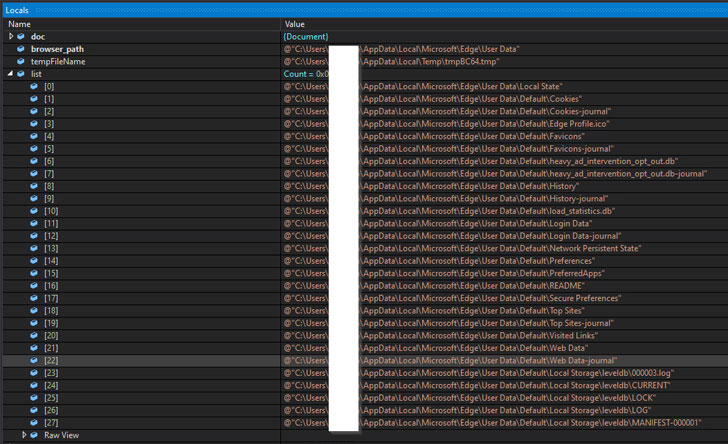
It’s known for its information stealing and backdoor features,
enabling the attackers to steal data stored in web browsers and
execute arbitrary commands retrieved from a remote server.
In February 2022, the operators of SolarMarker were observed[2]
using stealthy Windows Registry tricks to establish long-term
persistence on compromised systems.
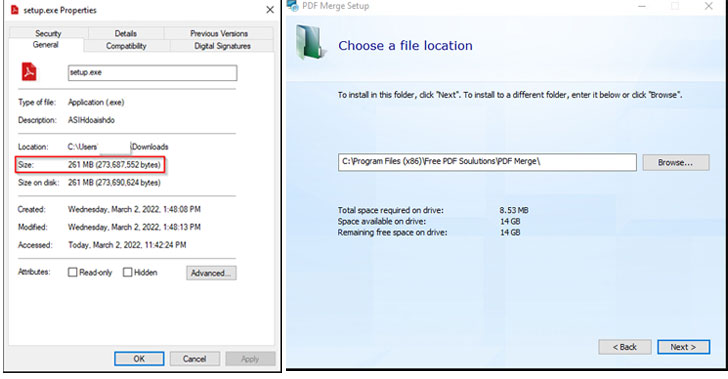
The evolving attack patterns spotted by Unit 42 are a
continuation of this behavior, what with the infection chains
taking the form of 250MB executables for PDF readers and utilities
that are hosted on fraudulent websites packed with keywords and use
SEO techniques to rank them higher in the search results.
The large file size not only allows the initial stage dropper to
avoid automated analysis by antivirus engines, it’s also designed
to download and install the legitimate program while, in the
background, it activates the execution of a PowerShell installer
that deploys the SolarMarker malware.
A .NET-based payload, the SolarMarker backdoor is equipped with
capabilities to conduct internal reconnaissance and vacuum system
metadata, all of which is exfiltrated to the remote server over an
encrypted channel.
The implant also functions as a conduit to deploy the
SolarMarker’s information-stealing module on the victim machine.
The stealer, for its part, can siphon autofill data, cookies,
passwords, and credit card information from web browsers.
“The malware invests significant effort into defense evasion,
which consists of techniques like signed files, huge files,
impersonation of legitimate software installations and obfuscated
PowerShell scripts,” the researchers said.
Read more https://thehackernews.com/2022/04/new-solarmarker-malware-variant-using.html