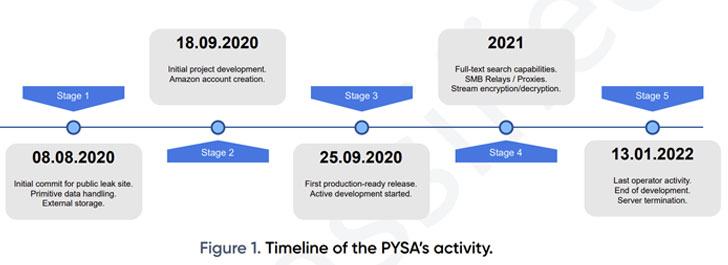
An 18-month-long analysis of the PYSA ransomware operation has
revealed that the cybercrime cartel followed a five-stage software
development cycle from August 2020, with the malware authors
prioritizing features to improve the efficiency of its
workflows.
This included a user-friendly tool like a full-text search
engine to facilitate the extraction of metadata and enable the
threat actors to find and access victim information quickly.
“The group is known to carefully research high-value targets
before launching its attacks, compromising enterprise systems and
forcing organizations to pay large ransoms to restore their data,”
Swiss cybersecurity company PRODAFT said[1]
in an exhaustive report published last week.
PYSA, short for “Protect Your System, Amigo” and a successor of
the Mespinoza ransomware, was first observed in December 2019 and
has emerged as the third most prevalent ransomware strain detected
during the fourth quarter of 2021.
Since September 2020, the cybercriminal gang is believed to have
exfiltrated sensitive information belonging to as many as 747
victims until its servers were taken offline earlier this
January.
Most of its victims are located in the U.S. and Europe, with the
group primarily striking government, healthcare, and educational
sectors. “The U.S. was the most-impacted country, accounting for
59.2% of all PYSA events reported, followed by the U.K. at 13.1%,”
Intel 471 noted[2]
in an analysis of ransomware attacks recorded from October to
December 2021.
PYSA, like other ransomware families, is known to follow the
“big game hunting” approach of double extortion, which involves
publicizing the stolen information should a victim refuse to comply
with the group’s demands.
Every eligible file is encrypted and given a “.pysa” extension,
decoding which requires the RSA private key that can only be
obtained after paying the ransom. Almost 58% of the PYSA victims
are said to have made digital payments.
PRODAFT, which was able to locate a publicly available .git
folder managed by PYSA operators, identified one of the project’s
authors as “dodo@mail.pcc,” a threat actor who is believed to be
located in a country that observes daylight savings time based on
the commit history.
At least 11 accounts, a majority of which were created on
January 8, 2021, are said to be in charge of the overall operation,
the investigation has revealed. That said, four of these accounts —
named t1, t3, t4, and t5 — account for over 90% of activity on the
group’s management panel.
Other operational security mistakes made by the group’s members
also made it possible to identify a hidden service running on the
TOR anonymity network — a hosting provider (Snel.com B.V.) located
in the Netherlands — offering a glimpse into the actor’s
tactics.
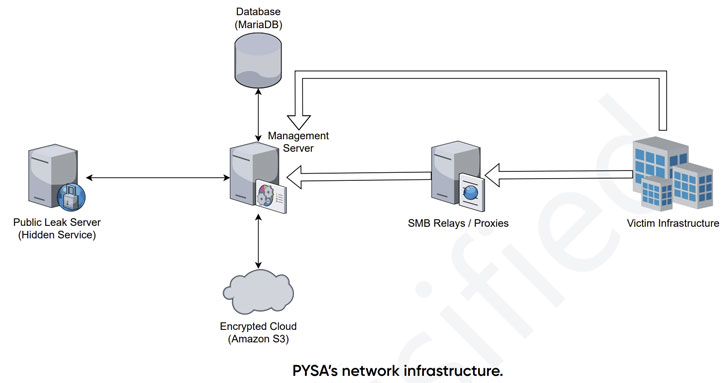
PYSA’s infrastructure also consists of dockerized containers,
including public leak servers, database, and management servers, as
well as an Amazon S3 cloud to store the encrypted files, which
amount to a massive 31.47TB.
Also put to use is a custom leak management panel to search
confidential documents in the files exfiltrated from victims’
internal networks prior to encryption. Besides using the Git
version control system to manage the development processes, the
panel itself is coded in PHP 7.3.12 using the Laravel
framework.
What’s more, the management panel exposes a variety of API
endpoints that enables the system to list files, download files,
and analyze the files for full-text search, which is designed to
categorize the stolen victim information into broad categories for
easy retrieval.
“The group is supported by competent developers who apply modern
operational paradigms to the group’s development cycle,” the
researcher said. “It suggests a professional environment with
well-organized division of responsibilities, rather than a loose
network of semi-autonomous threat actors.”
If anything, the findings are yet another indicator that
ransomware gangs like PYSA and Conti operate and are organized[3]
like legitimate software companies[4], even including[5]
an HR department to recruit new hires and an “employee of the
month” award for tackling challenging problems.
The disclosure also comes as a report from cybersecurity company
Sophos found[6]
that two or more threat actor groups spent at least five months
within the network of an unnamed regional U.S. government agency
before deploying a LockBit ransomware payload at the start of the
year.
References
Read more https://thehackernews.com/2022/04/researchers-share-in-depth-analysis-of.html