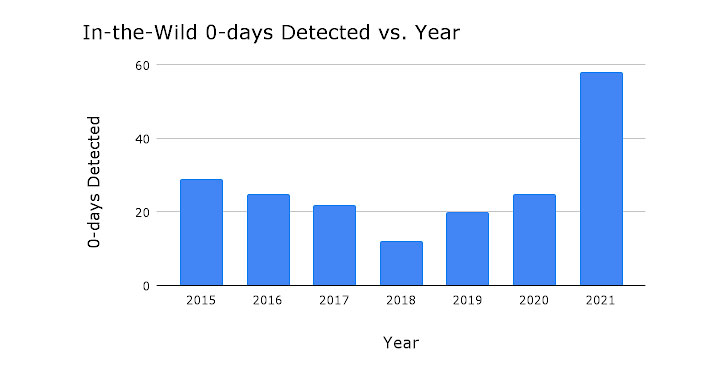
Google Project Zero called 2021 a “record year for in-the-wild
0-days,” as 58 security vulnerabilities[1] were detected and
disclosed during the course of the year.
The development marks more than a two-fold jump from the
previous maximum when 28 zero-day exploits were tracked in 2015. In
contrast, only 25 zero-day exploits were detected in 2020.
“The large uptick in in-the-wild 0-days in 2021 is due to
increased detection and disclosure of these 0-days, rather than
simply increased usage of 0-day exploits,” Google Project Zero
security researcher Maddie Stone[2]
said[3].
“Attackers are having success using the same bug patterns and
exploitation techniques and going after the same attack surfaces,”
Stone added.
The tech giant’s in-house security team characterized the
exploits as similar to previous and publicly known vulnerabilities,
with only two of them markedly different for the technical
sophistication and use of logic bugs to escape the sandbox.
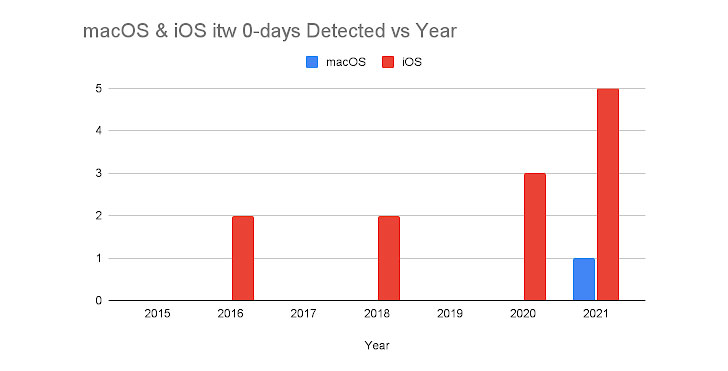
Both of them relate to FORCEDENTRY[4], a zero-click iMessage exploit[5] attributed to the
Israeli surveillanceware company NSO Group. “The exploit was an
impressive work of art,” Stone said.
The sandbox escape is “notable for using only logic bugs,”
Google Project Zero researchers Ian Beer and Samuel Groß explained[6]
last month. “The most striking takeaway is the depth of the attack
surface reachable from what would hopefully be a fairly constrained
sandbox.”
A platform-wise breakdown of these exploits shows that most of
the in-the-wild 0-days originated from Chromium (14), followed by
Windows (10), Android (7), WebKit/Safari (7), Microsoft Exchange
Server (5), iOS/macOS (5), and Internet Explorer (4).
Of the 58 in-the-wild 0-days observed in 2021, 39 were memory
corruption vulnerabilities, with the bugs stemming as a consequence
of use-after-free (17), out-of-bounds read and write (6), buffer
overflow (4), and integer overflow (4) flaws.
It’s also worth noting that 13 out of the 14 Chromium 0-days
were memory corruption vulnerabilities, most of which, in turn, are
use-after-free vulnerabilities.
What’s more, Google Project Zero pointed out the lack of public
examples highlighting in-the-wild exploitation of zero-day flaws in
messaging services like WhatsApp, Signal, and Telegram as well as
other components, including CPU cores, Wi-Fi chips, and the
cloud.
“This leads to the question of whether these 0-days are absent
due to lack of detection, lack of disclosure, or both?,” Stone
said, adding, “As an industry we’re not making 0-day hard.”
“0-day will be harder when, overall, attackers are not able to
use public methods and techniques for developing their 0-day
exploits,” forcing them “to start from scratch each time we detect
one of their exploits.”
References
- ^
58
security vulnerabilities (docs.google.com) - ^
Maddie
Stone (www.wired.com) - ^
said
(googleprojectzero.blogspot.com) - ^
FORCEDENTRY
(thehackernews.com) - ^
zero-click iMessage exploit
(googleprojectzero.blogspot.com) - ^
explained
(googleprojectzero.blogspot.com)
Read more https://thehackernews.com/2022/04/google-project-zero-detects-record.html